Cyber Risk in 2026: Top Threats, AI Risks & What Security Leaders Must Do Next
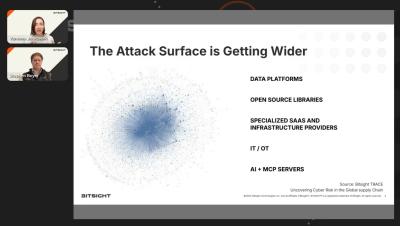
Cyber risk is evolving fast—and 2026 will demand more from security leaders than ever before. In this forward-looking webinar, Bitsight Co-Founder Stephen Boyer and SVP Vanessa Jankowski break down the biggest cyber threats shaping the year ahead, from AI-driven attacks and expanding attack surfaces to third-party and cloud risk.