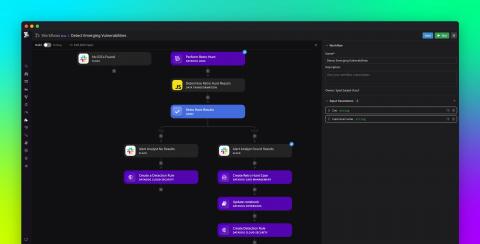
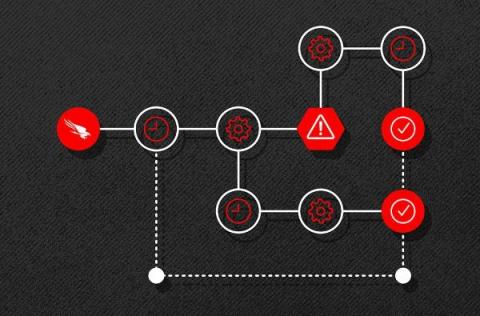
Automate common security tasks and stay ahead of threats with Datadog Workflows and Cloud SIEM
Detecting and remediating security threats is a constantly evolving concern for modern DevSecOps and security operations center (SOC) teams. Moreover, manually investigating and responding to vulnerabilities and threats is time-consuming, laborious, and knowledge-intensive.