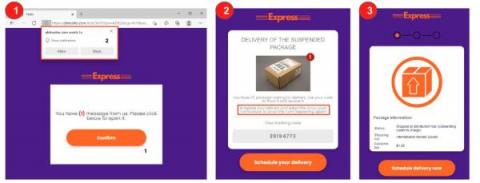
FedEx Phishing Campaign Abusing TrustedForm and PAAY
Netskope Threat Labs is tracking a phishing campaign that mimics a FedEx package delivery as bait to steal credit card data. This type of social engineering attack is commonly found in phishing pages, emails, and other scams, where a false sense of urgency is created to urge the victim into doing an action that eventually leads to personal data theft.