CloudCasa + Red Hat OpenShift: Unstoppable Data Protection for Hybrid Cloud Workloads
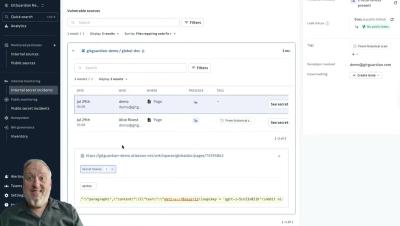
CloudCasa delivers certified, enterprise-grade data protection for Red Hat OpenShift across private, public, and edge environments. Protect VMs and containers with immutability, encryption, and isolated management domains. Gain reliable backups, disaster recovery, and migration across multi-cluster, multi-cloud, and multi-tenant setups. With automation-first design, zero-touch agents, and advanced recovery options, CloudCasa ensures your workloads are secure, recoverable, and portable—without limits.