Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Why You Should Get Started with the Rego Policy Language
The Rego policy language is the backbone of Open Policy Agent (OPA), the policy enforcement tool that helps simplify cloud-native development at scale. With OPA Rego policy, the result is a reduced manual authorization burden, improved accuracy, and quicker time to market. But yes, there’s a learning curve, which makes Rego a main barrier to using OPA. You might be hesitant about the time investment needed to learn a new, highly specified language.
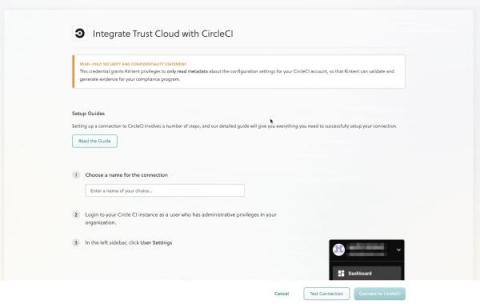
New Integrations Just Announced: CircleCI and Travis CI
Since working on a spreadsheet, you and your team have come a long way. You’re enjoying the ease of working in TrustOps because it automates control mapping, test creation, and evidence workflows. However, you’re looking for ways to save a bit more time, so you can focus on your day job and growing list of priorities. Collecting evidence to validate compliance controls takes time and affects your team’s productivity, including HR, IT, and DevOps.
Kubernetes version 1.25 - everything you should know
Group Policy Guide for Baseline Hardening
Vulns Unleashed: Dompdf
Code repository scanning & Container image registry scanning with Kubescape
Mining Malware History for Clues on Malicious Package Innovation
Malware has come a long way since it first made the scene in the late 1990s, with news of viruses infecting random personal computers worldwide. These days, of course, attackers have moved beyond these humble roots. Now they deploy a variety of innovative techniques to extract large amounts of money from businesses around the world. A similar development is taking place with malware’s upstart cousin – the emergence of malicious packages being uploaded to package registries.
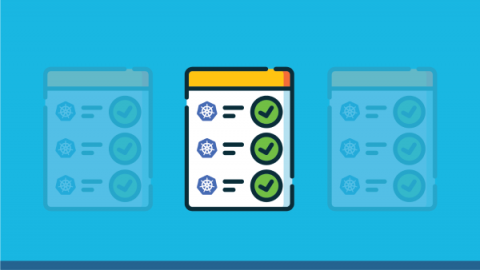
The One-Stop Kubernetes Security Checklist
Securing your Kubernetes environments may seem daunting at first, given how many different parts must be individually protected. Still, with the proper organization, you can make Kubernetes security much simpler and more effective. We’ve put together a complete Kubernetes security checklist of best practices and security recommendations to help you keep track of your progress. To make this a little easier, we’ve divided this checklist into the following sections.