Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Making Cal-Secure Work for California Government Agencies
Complying with the National Cybersecurity Authority Regulations
List of Cybersecurity Laws and Regulations in the UK
The digital threat landscape in the United Kingdom (UK) continues to evolve as businesses that undergo a massive transition towards increased digitalization and cloud-based migrations are forced to change their IT system operations. More importantly, UK laws and regulations must also adapt to ensure that UK businesses and organizations are working to improve their cybersecurity posture and IT infrastructure to protect data security and privacy.
Compliance and adoption for companies using the Cloud
Cloud adoption and use in corporate environments are rising, and its future looks bright. Business spending on Cloud services indicates this upward trend, as it increased by 29% in the second quarter of the year compared to the same period last year. Cloud migration has ushered in changes to regulations to consolidate data security according to the nature of the business.
Vulnerability scanning tools: What are they and how should they be used?
Part of the challenge of creating a robust security posture is collecting the right toolbox full of tools and services. There’s a wide world out there full of tools that can enhance your security, but one of the most productive types of tools every organization needs is a vulnerability scanning tool. To help you navigate these types of tools and recognize how they fit into your information security system, we’re taking a closer look at these tools and how they work.
Make Compliance a Breeze with Modern Log Management
From manufacturers in Michigan to fintechs in Finland, every business must comply with industry regulations — which are increasingly constraining. At the same time, businesses must protect and account for a growing number of systems, applications and data in order to remain compliant. In other words, compliance is getting harder. Enter log management. While regulations vary by country and industry, nearly every organization must store compliance-relevant information for a certain period of time.
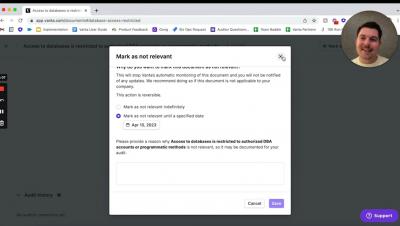
New in Vanta | January 2023
It’s been a busy start of the year for Vanta. We’ve made some major additions and improvements, such as our acquisition of Trustpage, as well as some exciting platform updates:
ISO 27001 welcomes Threat Intelligence
In my previous article I defined what is Cyber Threat Intelligence (CTI), described how to measure it and explained why it is important to implement a CTI program that can serve different stakeholders with different types of intelligence requirements in order to have a proactive security approach. 2022 was a productive year for ISO (International Organization for Standardization) security standards.