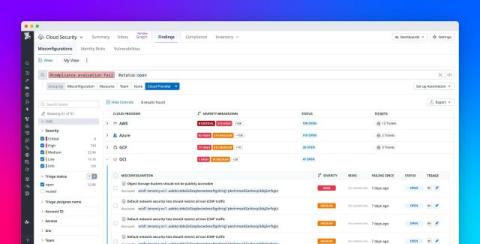
From the endpoint to the prompt: a unified data security vision in Cloudflare One
Cloudflare One has grown a lot over the years. What started with securing traffic at the network now spans the endpoint and SaaS applications – because that’s where work happens. But as the market has evolved, the core mission has become clear: data security is enterprise security. Here’s why. We don’t enforce controls just to enforce controls.