Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
April 2021
Dynamic Observability: Troubleshooting Techniques for 2021
Open Banking Opportunities to Retain and Delight Existing Customers
The banking landscape is changing. The days of walled garden banking where customers can’t see or access information from all their financial institutions in one place are coming to a close. For banks, and the entire financial services industry, open banking isn’t a threat but a customer service opportunity. Instead of putting barriers between customers and their financial information at other institutions, banks can offer value-added insights across accounts and institutions.
Detect unauthorized third parties in your AWS account
Detecting when an unauthorized third party is accessing your AWS account is critical to ensuring your account remains secure. For example, an attacker may have gained access to your environment and created a backdoor to maintain persistence within your environment. Another common (and more frequent) type of unauthorized access can happen when a developer sets up a third-party tool and grants it access to your account to monitor your infrastructure for operations or optimize your bill.
MITRE Engenuity ATT&CK Round 3: Carbanak + FIN7 vs. the free and open capabilities in Elastic Security
Whether this is the third time you are looking at the MITRE Engenuity ATT&CK® evaluation results or your first, you may be asking yourself: what was unique about this year’s evaluation? Well, let’s first start with: who is MITRE Engenuity? They are a tech foundation that collaborates with the private sector on many initiatives — most notably cybersecurity — and in recent years have become synonymous with cyber threat evaluations.
Introducing AT&T's Managed Endpoint Security with SentinelOne
With 5G, edge solutions, and digital transformation all around us, every enterprise should be taking a closer look at their endpoint security and evaluate options that will be able to keep pace with this dynamic new environment.The newly introduced AT&T Managed Endpoint Security with SentinelOne™ offer brings world class managed services with comprehensive endpoint security.
Agentless Monitoring with Tripwire Enterprise: What You Need to Know
As we know, Tripwire Enterprise (TE) is the de-facto go-to solution for File Integrity Monitoring (FIM). In normal operations, we deploy a TE agent to a system we want to monitor. TE then uses that agent to baseline the system against the appropriate rules, creating a known good state for that system. Moving forward, that system is monitored for change per the rules that were used to create the baseline.
Detect anomalous activity in your environment with new term-based Detection Rules
When it comes to securing your production environment, it’s essential that your security teams are able to detect any suspicious activity before it becomes a more serious threat. While detecting clear-cut attacker techniques is essential, being able to spot unknowns is vital for full security coverage.
Bits of Security, Security Panel
Bits of Security
Securing Your Supply Chain with CIS and Tripwire
Where were you when you first heard about the SolarWinds breach? It’s not unusual for information security professionals to learn about a breach. Keeping track of the news is part of the job. The SolarWinds attack, however, was different for two primary reasons. First, it reached the level of mainstream news. The majority of breaches stay mostly in the industry press.
Protecting Your Electronic Health Records (EHR) With Continuous Monitoring
After a year of lockdown, or nearly full lockdown, due to the ongoing health crisis, we learned a lot from how our organizations responded when we all had to change our work habits to a home-office setup.
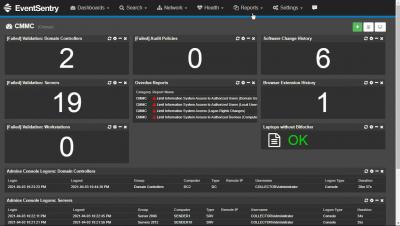
Why You Need to Closely Monitor Your Exchange Servers
Monitoring your on-prem and hybrid cloud infrastructure has always been important. With an ever-growing rise in cyber attacks, zero-day exploits, and insider threats, keeping track of your infrastructure has a renewed level of significance. Microsoft Exchange is one of the most prominent enterprise systems in use today, with both cloud and on-prem iterations.
Bits of Security, Snyk.io: Stranger Danger: Finding Security Vulnerabilities Before They Find You!
Bits of Security, PedidosYa: Fraud Detection using Datadog and Sherlock
Datadog acquires Sqreen to strengthen application security
We began our security journey last year with the release of Datadog Security Monitoring, which provides runtime security visibility and detection capabilities for your environment. Today, we are thrilled to announce that Sqreen, an application security platform, is joining the Datadog team. Together, these products further integrate the work of security, development, and ops teams—and provide a robust, full-stack security monitoring solution for the cloud age.
What is a ROPA, why you need one, and how to make the process easier.
Working toward GDPR compliance means taking inventory on the data you collect and process. You've mapped your data, have a catalog of impact assessments, but now you need a way to present it in a way that regulators can look over. As far as the general data protection regulation (GDPR) is concerned, every piece of data processing you do needs a record, and those records are stored in a record of processing activities (ROPA). Regulators use a ROPA to get a full picture of your data processing.
How Tripwire Can Help U.S. Federal Agencies Implement the CIS Controls
Digital attackers are increasingly launching sophisticated campaigns in an effort to target U.S. federal agencies and other organizations. Two recent examples demonstrate this reality. These are the SolarWinds supply chain attack and the HAFNIUM Exchange exploit campaign.
Integrity: How It's More than Just Data Security and FIM
Integrity is a word thrown around a lot in the cybersecurity space. That’s not surprising. It is one of the three components that make up the CIA Triad, after all. However, the meaning and use of the word has been relatively limited in many security circles up until now. Let’s take a look at the security industry more broadly. In most conversations dealing with integrity, data security and File Integrity Monitoring (FIM) controls often end up being the primary focal areas.
What's the Most Powerful Tool in Your Security Arsenal?
Trying to work out the best security tool is a little like trying to choose a golf club three shots ahead – you don’t know what will help you get to the green until you’re in the rough. Traditionally, when people think about security tools, firewalls, IAM and permissions, encryption, and certificates come to mind. These tools all have one thing in common – they’re static.