Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
June 2024
Cyber Security Report Examples (3 Common Styles)
Cyber security reports are an invaluable tool for keeping stakeholders and senior management informed about your cyber security efforts. This post outlines examples of some of the most popular reporting styles, with a particular focus on a field of cybersecurity drawing increasing interest among executive teams - Vendor Risk Management. Each of the cyber security report examples in this list have been pulled from the UpGuard platform.
The IT Hour | Product Roadmap on JCU 06.21.24
Nate Copt joins to show us more on the new product roadmap in JumpCloud University. Join us at 11:30 am ET. The #IT Hour hosted by #JumpCloud is a #communityprogram focused on the life of #ITAdministrators. With the ever changing #ITlandscape, having community and professional networking opportunities is very valuable.
How to Get the IP Address of a Docker Container
Watch the full video for more...
Navigating the Hybrid Workplace: Balancing Productivity, Efficiency and Security
In today's digital workplace, we rely heavily on a wealth of collaboration solutions; in fact, these tools have become ingrained and part of our daily workflows. Despite hybrid working patterns and the return, for some, to a more traditional work environment, the continued reliance on collaboration apps remains strong. This presents opportunities and challenges for the IT teams tasked with onboarding and offboarding employees and effectively managing an ever-growing plethora of tools and apps.
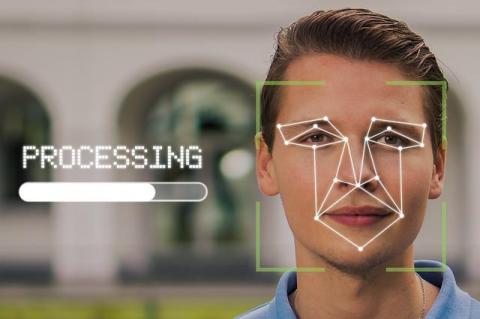
How to Use Facial Recognition for Face Search
The lives of modern people are becoming increasingly comfortable and productive, all thanks to the rapid advancement of innovative technologies. Nowadays, to communicate with acquaintances, make purchases, and pay for services, all you need to do is connect your device to the internet. Have you lost contact with an old acquaintance? This is easily remedied by Face search person by photo. The principle of search work is as simple as possible. To get the necessary information you should simply upload a photo to the search engine.
Top 10 Online Resources for Parents to Educate Themselves About Internet Safety
In today's digital age, ensuring internet safety for children is more critical than ever. The online world offers a vast landscape of opportunities and information, but it also exposes kids to harmful online content that parents need to guard against. Here, we aim to equip parents with the best online resources to educate themselves about internet safety. We'll explore a variety of tools, guides, and courses that provide essential knowledge and strategies to keep your children safe online.
Public Sector Breach Alert: Q2 2024
The public sector continues to be a target for cybercriminals as ransomware attacks and data breaches hit government organizations at all levels, incurring large financial costs and operational disruptions. The public sector is especially vulnerable to cyber attacks for a variety of reasons, including legacy systems, lack of resources, large amounts of sensitive data and the fact that it manages essential services.
What I Did To Secure My Accounts After the Ticketmaster Breach
On May 20, 2024, Ticketmaster parent company Live Nation Entertainment launched an investigation after detecting unauthorized activity within a database containing company data. A week later, they were contacted by someone who threatened to sell their user data on the dark web. I, like many other Ticketmaster customers, became worried about my data, so I took immediate steps to protect myself. Here is what I did.
How To Disable Your Browser-Based Password Manager
If you save your passwords in a browser password manager, your passwords may be at risk of becoming compromised. This is because browsers frequently remain logged in, meaning if someone gained access to your device they’d have access to all your stored passwords. Additionally, if your browser were to become compromised, everything stored in your browser would also be at risk of becoming compromised due to weak encryption standards.
Why Vulnerability Scanning is an Offensive Security Program's Secret Weapon
Knowing what you don’t know is the key to keeping an organization safe and the best method of doing so is with an offensive security approach that includes vulnerability scanning. By being proactive one can identify exploitable weaknesses in your own systems before malicious actors can. Here's why vulnerability scanning is an essential part of any offensive security solution: Vulnerability scanning is just one piece of the offensive security puzzle, but it's a crucial one.
Tech Talk: Abusing ESC13 from Linux
This is a Bulletproof Tech Talk article: research from our penetration testing team covering issues, news, and tech that interests them. It’s more technical and in-depth that our usual blog content, but no less interesting. In the complex landscape of Active Directory, ensuring secure and appropriate access is a constant challenge. Recently another "ESC" technique has been released which is known as ESC13.