Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Cybersecurity from an overhead cost to a business enabler
Implementing cybersecurity projects shouldn’t only depend on return on investment or viewed as a cost. There’s a better way you could be evaluating it. Businesses should be thinking about how adding cybersecurity can add more business value and enable company growth. The landscape is changing and security is starting to be seen as a competitive advantage more often, and for some industries, it’s a reason customers want to do business with a brand.
Detectify releases API v2.5
Security should be easy to integrate into the development cycle, which is why we offer our Detectify API integration for ease of managing your automated security workflow. Today we’ve released Detectify API v2.5 with improvements that allow API users to maximize automation you can get from Detectify.
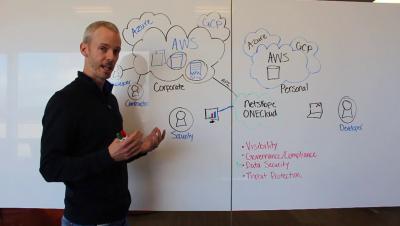
A Multi-Million Dollar Commitment to Our Multi-Cloud Strategy
Every business today is growing in their own unique way. Their infrastructure is made up of a combination of cloud and on-premises repositories. Their application suite is custom built with a myriad of productivity applications like Slack, Office 365, Zoom, and more. And finally, their users are working on a wide range of devices, from Apple iPhones to Microsoft Surface Pros. The common theme amongst businesses is their need for flexibility.
Understanding Software Exploit Scoring Today
Even with years of related industry experience an individual can become lost in all of the acronyms surrounding security vulnerabilities in modern software. Several of these acronyms exist, and many of them are very similar. Some of the most common are discussed below.
Securing GCP: Top 10 Mistakes to Avoid
Securing People
Cybersecurity has three pillars of people, process, and technology. Enterprises have historically had a skewed focus towards the technology aspect of cyber security - installing another endpoint agent, or deploying another network monitoring device designed to seek out anomalys behaviour.
Smart Cloud Sessions: Protecting sensitive data in Public Cloud Infrastructure
AWS System Manager And The Dangers of Default Permissions
In September of 2018, Amazon Web Services (AWS) announced the addition of the Session Manager to the AWS Systems Manager. The session manager enables shell or remote desktop level access to your AWS EC2 Windows and Linux instances, along with other benefits. This is a great new feature, but care should be taken when enabling this capability.
New Tigera Secure Enterprise 2.3 Anomaly Detection Deepens Visibility into Suspicious Kubernetes Activities
Tigera is excited to announce several new capabilities with Tigera Secure Enterprise Edition 2.3, extending the ability to uncover sophisticated Kubernetes attacks. Tigera Anomaly Detection capabilities provide insight into unusual behaviors that compromise the security and performance of Kubernetes environments.
How to Initiate a Threat Hunting Program (Part 1)?
Over the past many years, cyber threats have become greater in frequency and more sophisticated than ever. Current security mechanisms are based on traditional reactive approaches such as antivirus programs and firewalls who react once the incident has occurred. Under such circumstances, intruders have a chance to compromise your network either partially or entirely.