Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Securing the digital supply chain Ep 7 Yaser M
What the sysadmin misses, Desktop Central catches!
Most people are fairly good at reading, but not enough are good at reading between the lines. More often than not, there are certain things hidden in plain sight that may not catch your attention. The eyes of a system administrator are often glued to tasks like system maintenance and user administration. When engaged in many tasks at once, it is only human to overlook a few things like patch and antivirus updates, but it can cost an organization dearly in terms of data security.
Three things you should know about SASE and SD-WAN
As organizations have accelerated their plans to better enable dispersed workforces in a post-pandemic reality, many technology decision-makers are broadly rethinking their network architectures. Inevitably their discussions lead to comparisons and debates over both software-defined wide area network (SD-WAN) and secure access service edge (SASE) technologies.
Leaving your job? Here's how to protect yourself and your employer's data
The end is in sight. You’ve decided to leave your job and have already handed in your notice. You’re finishing up some final projects and, before too long, will be saying one last goodbye to your coworkers.
What Is Cyber Hygiene?
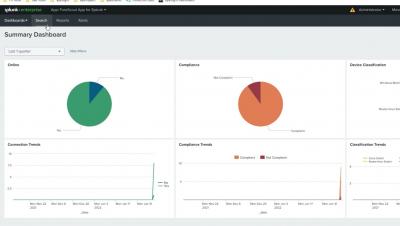
How To: Configure Splunk & Forescout Integration
Teaming up with Sysdig to deliver developer and runtime Kubernetes security
Today, we’re excited to announce a partnership with Sysdig to provide container and Kubernetes security together — from code to cluster. Together, Snyk and Sysdig can help developers secure code and containers in development, protect the runtime Kubernetes environment, and deliver feedback and visibility from production back to developers, eliminating the noise of container vulnerabilities.
SAST vs. SCA: 7 Key Differences
Everybody’s talking about securing the DevOps pipeline and shifting security left.. AppSec tools like SAST (Static Application Security Testing), DAST (Dynamic Application Security Testing), and others that address issues in proprietary software have become staples of the developer’s security toolbox.
Defend Against Ransomware and Malware with Falcon Fusion and Falcon Real Time Response
Adversaries are moving beyond malware and becoming more sophisticated in their attacks by using legitimate credentials and built-in tools to evade detection by traditional antivirus products. According to the CrowdStrike 2022 Global Threat Report, 62% of detections indexed by the CrowdStrike Security Cloud in Q4 2021 were malware-free.