Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
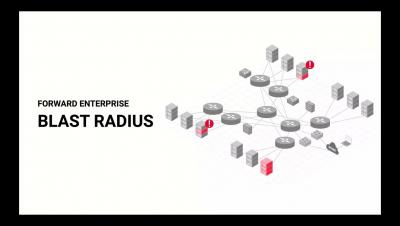
Assessing Infected IP damage with Blast Radius
Lessons From Billions of Breached Records by Troy Hunt of https://haveibeenpwned.com
Securing SAP SuccessFactors: Best Practices to Stay Compliant
Breaking the Chain: Are You the Unintended Victim of a Supply Chain Attack?
We’ve heard a lot about “supply chains” of various industries over the past couple of years, and the cybersecurity sector is no exception. When Colonial Pipeline was compromised by ransomware, it affected the physical supply of gasoline to consumers. On the software side, malware distributed through a SolarWinds update and vulnerabilities discovered in Apache’s Log4J created rippling effects for organizations around the world.
Security Service Edge (SSE) is a Profound Moment for Cloud, Data, and Network Security
Today we are very excited to share that Netskope has been named a Leader in the 2022 Gartner ® Magic Quadrant ™ for Security Service Edge (SSE). This Magic Quadrant for SSE* is the first such SSE analysis of its kind, and I invite you to read the full SSE report (available here) to learn how Netskope was recognized for its completeness of vision and ability to execute.
Best Go Regex Library
Skip below to the results, otherwise read on to learn more about our specific use case.
FedRAMP Terminology
Just like any compliance or set of regulations, FedRAMP uses many acronyms and key terms to describe processes, standards, and regulations. This article explains key terminology that is used in the FedRAMP framework. You may already be familiar with some of these compliance terms and acronyms from other security frameworks.
FedRAMP Cloud Service Providers and Services
Google adopted its cloud infrastructure, Google Cloud Platform (GCP), to be compliant with FedRAMP. GCP earned a FedRAMP High authorization to operate (ATO) for several cloud products in a handful of locations and has uplifted the current FedRAMP Moderate services to more products and locations. Government agencies can now work with the highest level of classified information using GCP.
OSCAL and FedRAMP Automation
The current FedRAMP Authorization process is a struggle. First, you must manage multiple regulatory standards and frameworks, which change over time. Second, regulatory standards and frameworks overlap in scope and can often conflict and be difficult to manage together. And, lastly, information systems continue to increase in size and complexity.
Most Common Authentication Vulnerabilities
The majority of threats related to the authentication process are associated with passwords and password-based authentication methods. But broken authentication also causes a significant amount of vulnerabilities. Broken authentication occurs when the implementation of the authentication process is flawed. Unfortunately, this is usually hard to discover, and can be more severe than the risks associated with passwords.