Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
What's next for digital currencies?
Over the last two years, we’ve observed how digital assets have revolutionized payment and banking services. The explosion of interest in digital currencies brings with it new challenges in governance, privacy, competition, cybersecurity, and social inclusion. While a cashless future is still far away, more than 80% of central banks are either considering the launch of a central bank digital currency (CBDC) or have already done so.
Building a secure API with gRPC
A Google remote procedure call (gRPC) is Google’s open source version of the remote procedure call (RPC) framework. It’s a communication protocol leveraging HTTP/2 and protocol buffer (protobuf) technologies. gRPC enables a remote client or server to communicate with another server by simply calling the receiving server’s function as if it were local. This makes communicating and transferring large data sets between client and server much easier in distributed systems.
The ReadOut: Falcon Long Term Repository
Rubrik and GraphQL - Episode 5 - Interfaces and Inline Fragments
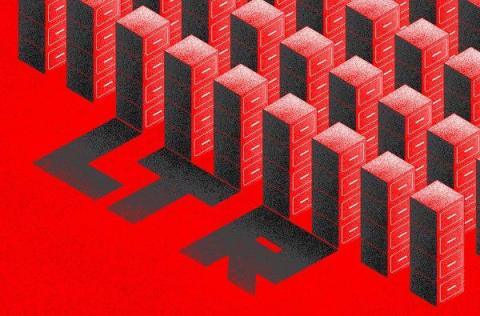
What is the Dark Web?
The dark web is a part of the internet that provides anonymous and secure communication channels that are not able to be found by search engines. Numerous criminal activities are carried out on the dark web, such as the trafficking of stolen personal information, illegal sales of weapons and the trafficking of drugs.
Getting Started Guide: Falcon Long Term Repository
Limited data retention resulting from financial or technological constraints makes it hard for security teams to see the complete history of an attack. This lack of full context about a threat — or a potential threat — eventually catches up with organizations, leading to longer dwell times and increased risk of a breach.
Securing Cloud Infrastructure with Teleport and AWS Identity Federation
Over the last decade, enterprises have accelerated the adoption of the cloud. According to the State of the Cloud report by Flexera, the average annual spend on cloud computing is over $62 million. As enterprises continue to invest in the cloud, AWS, the market leader in cloud computing, is growing at a rapid pace. The rise of cloud computing poses new challenges to enterprise IT. With each department migrating and managing their workloads in AWS, there is a proliferation of accounts, users and roles.
Ransomware in Healthcare: The NHS Example and What the Future Holds
On August 4, 2022, Advanced – a major software provider for the UK’s National Health System (NHS) and other healthcare customers – suffered a ransomware attack from a group that is still unknown to the public. The attack disrupted NHS services including ambulance dispatch, appointment bookings, patient referrals and emergency prescriptions.
Key Metrics for Tracking PCI DSS Compliance in 2022
PCI DSS compliance ensures your customer’s credit card data is protected from hackers and compromise attempts. Though complying with this regulation isn’t easy, it is possible. To simplify this essential effort, we’ve compiled a checklist of the key security metrics that should be addressed to meet the compliance requirements of this critical information security standard.
NIST 800-171 Compliance Checklist (Free)
NIST compliance is mandatory for any entity and service provider processing Controlled Unclassified Information (CUI) on behalf of the US Federal Government. Given the substantial risk to national security if this sensitive data is exploited and the high potential of its compromise through supply chain attacks, the range of organizations expected to comply with this cybersecurity regulation is intentionally broad.