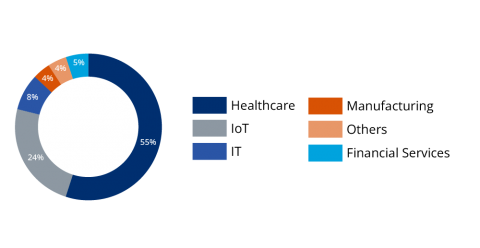
Moving Your Healthcare Organization to the Cloud? Here's What You Need to Know First
While the last two years accelerated digital transformation across a wide range of industries, this has been a long time coming for healthcare. Healthcare has been undergoing a massive shift to improve security, streamline operations, and enhance the patient experience—and much of that shift centers around the movement to the cloud. Cloud-native ostensibly offers a better, more accessible user experience marked by enhanced uptime, reliability, and efficiency.