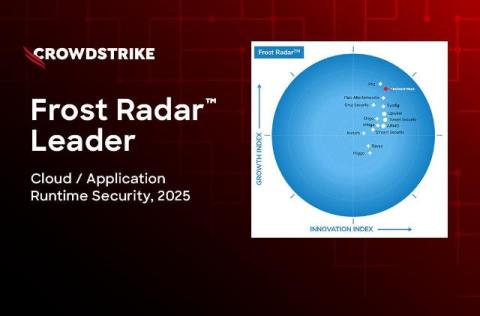
CrowdStrike Named a Frost Radar Leader in Cloud and Application Runtime Security
CrowdStrike has been named an innovation and growth Leader in the inaugural 2025 Frost Radar: Cloud and Application Runtime Security (CARS), positioned highest on the Innovation Index among all vendors evaluated. This marks another milestone in our mission to stop breaches with the industry's most unified and comprehensive cloud runtime protection.