Data Security in Collaborative Environments: Why Data Discovery and Protection Matter
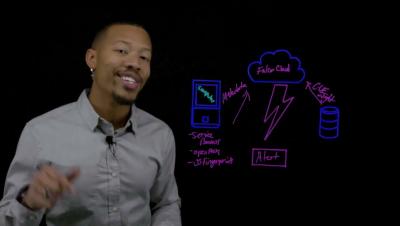
The LA Times recently reported on a suspected breach involving a public sector legal office and a third-party tool used to transfer discovery materials. According to the report, the exposed data included a large volume of highly sensitive records, including witness information, medical data, unredacted legal documents, personnel records, and investigative materials. Without getting ahead of the facts, there is a pretty straightforward lesson here. Sensitive data rarely stays in one place.