Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
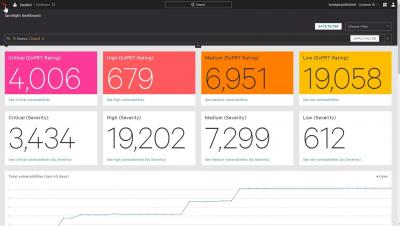
How to Automate Workflows with Falcon Spotlight
Preview-Only Links
Between Two Cones | Mitigating Construction Project Risks with CCPI
U.S. government warns that sensitive data is being stolen from defence contractors
The Federal Bureau of Investigation (FBI), Department of Homeland Security Cybersecurity and Infrastructure Security Agency (CISA), and National Security Agency (NSA) have joined forces to publish a joint warning that Russian hackers have targeted defence contractors to steal sensitive data.
Calico Cloud: Active build and runtime security for cloud-native applications
Calico Cloud has just celebrated its 1-year anniversary! And what better way to celebrate than to launch new features and capabilities that help users address their most urgent cloud security needs. Over the past year, the Tigera team has seen rapid adoption of Calico Cloud for security and observability of cloud-native applications.
What is Security Service Edge?
Creating Buy-In for a Cybersecurity Awareness Program
There is more to implementing a successful cybersecurity training program than to task IT with the job or conduct a quick Internet search to find an outside vendor. In a day and age when an employee’s error can lead to a disastrous cyberattack, it is imperative organizations have a basic understanding of how to implement an awareness program that reaches all employees, is conducted at the correct pace by well-informed instructors and is helpful, informative, and not irritating.
How to protect your sensitive data with automatic classification and labeling
5 Ways Ransomware Can Negatively Impact Your Business
In the past year, virtually every day has brought news of another debilitating ransomware attack. And, in many of those attacks, there were key lessons that can be applied to companies like yours. This article will recap five real-life impacts of recent ransomware attacks. It will also provide best practices you can follow to prevent your organization from becoming a potential victim.