Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Future Of Security Operations Roadshow: Using Github For Automated Case Management
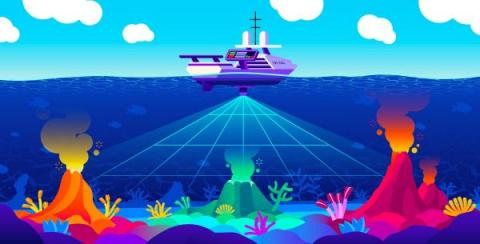
Shifting to Business Ecosystem Risk Management
Third-party risk management is a well-known industry term that emphasizes the importance of looking outside yourself to identify potential risks to your organization. In the current business landscape, where you are communicating and collaborating with dozens, if not hundreds, of other organizations, focusing on your own cyber risk and that of your third parties is not enough.
Best practices for detecting and evaluating emerging vulnerabilities
Identifying and evaluating security vulnerabilities is essential at every stage of software development and system management. New vulnerabilities surface all the time, demanding ongoing vigilance as well as effective methods of assessment and response. And recent data shows that this is increasingly the case.
The Dark Side of AI: ChatGPT and the Rise of Malware Ransomware
6 Australian Public Sector Cyber Trends to Watch in 2023
As AISA’s Cyber Conference 2023 being held in Canberra March 20-22 approaches, I thought I would go over some of the hot topics that I expect delegates from Australian public sector organizations will be talking about at the event. And just a quick aside, Trustwave is a keen sponsor of the baristas at this year’s Australian Cyber Conference and we hope to share a hot beverage (of your choice) with you, so please stop by to discuss some of the following hot button topics.
Navigating the security challenges of multi-tenancy in a cloud environment
Multi-tenancy can maximize the number of resources that are utilized in a cluster by sharing these resources between different groups, teams, or customers. However, boundaries must be placed to avoid problems associated with resource-sharing. On top of that, in a multi-tenant cluster, the number of security policies might gradually grow to the point where a slight misconfiguration could cause major security problems, performance issues, and service disruptions.
Fake ChatGPT apps spread Windows and Android malware
OpenAI's ChatGPT chatbot has been a phenomenon, taking the internet by storm. Whether it is composing poetry, writing essays for college students, or finding bugs in computer code, it has impressed millions of people and proven itself to be the most accessible form of artificial intelligence ever seen.
Finding YAML Injection with Snyk Code
I conducted some research to try and identify YAML Injection issues in open-source projects using Snyk Code. Though the vulnerability itself is not a new one, the potential impact of YAML Injection is high, which made it a good candidate for research. This research led to the discovery of several issues in open-source projects written in Python, PHP and Ruby. This article focuses on the issue found in geokit-rails version 2.3.2, a plugin for Ruby on Rails
CI/CD and the Promise of Agile Transformation
Continuous integration/continuous delivery (CI/CD), promises to help deliver software faster and more reliably. It does this by pushing frequent updates and fixes regardless of size and using automation tools to help the process run smoothly. According to Gartner, CI/CD is the most common agile practice currently being adopted by organizations. So how does CI/CD work and why is it critical for DevOps teams?