Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cybersecurity: When Stress and Trauma 'Get in the Way'
This blog contains a discussion about stress, trauma, and domestic violence. This may be difficult for some readers, and given the alarming figures around Post-Traumatic Stress Disorder (PTSD), trauma, and early life experiences (ACEs), this will likely concern at least a small population of readers. Please take care of yourself when reading this and break off from reading if you feel the need to.
The Essential Guide to Slack Data Loss Prevention (DLP)
DLP ensures confidential or sensitive information (like credit card numbers, PII, and API keys) isn’t shared outside of Slack by scanning for content within messages and files that break predefined policies. DLP is important for both security and compliance reasons. With DLP in place, you’ll be able to.
Kubernetes posture management - no time to waste time
Five months ago, we decided to release a posture management solution for K8s and make it open source for everyone to enjoy it.
What are the Types of Cyber Security Vulnerabilities?
As the threat landscape changes and advances with time, being able to address the most common types of cyber security vulnerabilities has gained the utmost importance. In this article, we will consider various types of cyber security vulnerabilities and how you can mitigate them. As information becomes an organization’s most important asset, cyber security gains increasingly more priority.
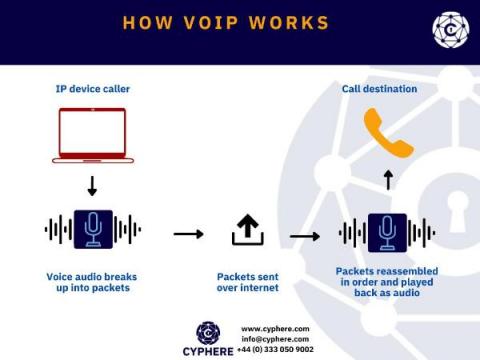
VoIP Security. How secure is your VoIP?
For over a century we have seen voice communication being made over Public Switched Telephone Network (PSTN), but since the past decade or two Voice over IP (VoIP) has been introduced and quickly adopted throughout the world for making business phone calls.
Cybersecurity Architecture: A Complete Guide to Preparing Your Organization for a Cyberattack
Weekly Cyber Security News 24/12/2021
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. Anyone fancy a bit of a challenge? USA citizens only though…