Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Student Verification: How Edtech can benefit from Student ID Verification APIs
Due to the growing acceptance of distance learning, digital courses, and most recently, the COVID-19 epidemic, online education has seen a significant increase. Online student identity verification has become more popular as a quick and secure method of verifying student IDs and a cost-effective approach to onboarding new students and employees. The rapidly disappearing manual and paper-based student verification procedures are neither scalable nor practical for educational institutions.
AvosLocker Ransomware Update: Backup Targeting and Defense Evasion Techniques
Kroll analysts have identified new tactics used by threat actors associated with the AvosLocker ransomware. Critical vulnerabilities have been exploited within Veeam Backup and Replication, which may be an attempt to hide activity from detection technologies. The proxy tool “Chisel” has been identified, which can encrypt traffic through a victim’s firewall and could be used as a further evasion technique.
Cyberattacks are targeting smaller healthcare companies and specialty clinics. But why?
The healthcare industry has been a favored target for cybercriminals for many years. In the first half of 2022 alone, 324 attacks against healthcare organizations have been reported. Attackers have primarily focused on large hospitals in years past, but there has been a sudden switch to smaller healthcare companies and specialty clinics. There seems to be a clear trend in attacks against the healthcare industry, and that trend includes targeting smaller healthcare companies and clinics.
Maintaining Boundaries Between Your Work and Personal Life as a Cybersecurity Professional
As the years go by, technology continues to evolve, and as we rely more and more on smart devices and the online space, there becomes greater risks of cyberattacks. If you work as a cybersecurity professional, then you are fighting the good fight, but it isn’t always easy. The job is unpredictable, and it requires odd hours and constant vigilance.
How Can You Comply With NRC RG 5.71?
In 1974, the United States Congress created the Nuclear Regulatory Commission (NRC) in order to protect the health of citizens and the environment while at the same time ensuring that radioactive materials were used in a safe manner for civilian purposes.
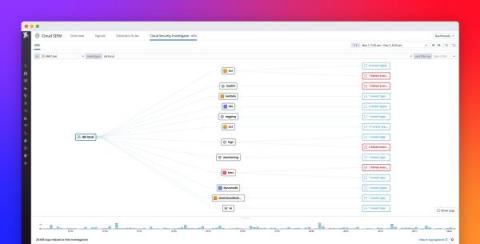
Visualize activity in your cloud environment with Datadog Cloud SIEM Investigator
Investigating the origin of activity in cloud-native infrastructure—and understanding which activity is a potential threat—can be a challenging, time-consuming task for organizations. Cloud environments are complex by nature, comprising thousands of ephemeral, interconnected resources that generate large volumes of alerts, logs, metrics, and other data at any given time.
Understanding alert overload part 2: How no-code automation can transform your security team
In a previous post, we discussed how alert overload can cripple security teams and prevent them from effectively detecting and responding to threats. In this post, we explore how no-code automation can help reduce the burden of alerts while providing the visibility and connectivity your organization requires. It's critical to have robust security solutions that not only help you detect but also block serious attacks before they cause any damage.
Can gamification unite development and security?
Despite years of effort encouraging a DevSecOps approach, development and security teams tend to remain divided. For example, according to 2020 research, 65% of security professionals reported that their companies had successfully shifted security left. Good, right? But the same research also shows that almost a third of people believe the security team is primarily responsible for security — despite shifting left.