What is DNS Spoofing?
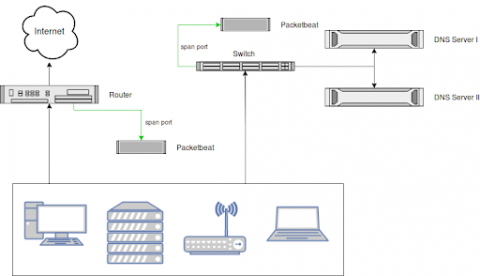
DNS spoofing, or DNS cache poisoning, is a cyber attack where false Domain Name System (DNS) information is introduced into a DNS resolver's cache. This causes DNS queries to return an incorrect response, which commonly redirects users from a legitimate website to a malicious website designed to steal sensitive information or install malware.