How effective is secure code review for discovering vulnerabilities?
We’ve recently discussed application security and the trend we’re seeing in which companies are increasingly implementing security early on in the Software Development Life Cycle (SDLC). In our blog post exploring the impact of adopting application security, we described a common scenario involving assessing an application that was ready for release. Through the assessment, critical vulnerabilities were identified, such as an SQL injection, close to the go-live deadline.
Netskope - The Undisputed Leader in the Evolution of CASB and Cloud Security
Cloud Access Security Brokers (CASB), also known as Cloud Security Gateways, were created to address the increasing cloud security problems facing organizations as cloud and application usage increased over the last decade.
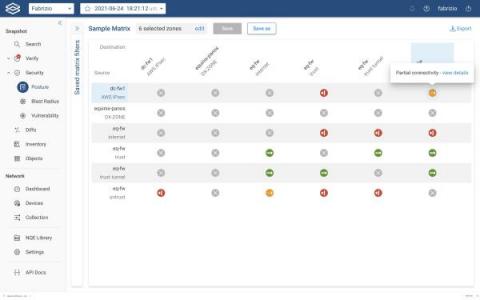
Where is Your Zone-to-Zone Connectivity Matrix?
If you’re like most of the complex IT shops we talk with, you probably don’t even have a current security matrix to store anywhere – file cabinet or data folder. The connectivity matrix is essentially the company security posture, but almost no one has a comprehensive way to visualize and easily understand the connectivity status between the various configured security policies (zone-to-zone policies).
Detecting CVE-2021-42292
On its surface, CVE-2021-42292 doesn’t look like the kind of vulnerability that a network-based tool can find reliably. Marked by Microsoft as a local file format vulnerability, security veterans would expect that between encryption and encoding, there would be a million different ways to evade network detection with a weaponized exploit.
What You Need to Remember When Choosing a Managed Service Provider (MSP)
In my previous post, I discussed some of the most common types of services offered by managed service providers (MSPs). This brings us to what organizations need to do to prepare to work with an MSP. Here are some considerations to keep in mind.
JUMPSEC The Team
ISO 27001 Compliance: What You Need to Know for Your Certification
Looking to become certified to the ISO 27001 standard? In this article you will learn what ISO 27001 is, the key terms and definitions, information security risks you need to consider, and the process for meeting your compliance and certification requirements.
Invest in Cyber Awareness to Prevent Attacks
Today’s cyber threat landscape is extremely challenging. Ransom this, ransom that, ransom everywhere – information technology (IT) professionals must work to protect organizations against the next big ransomware attack. Over the years, the sophistication of ransomware attacks has increased as well as the amount of money demanded and paid out in exchange for the ransom-held information.
Stories from the SOC - Powershell, Proxyshell, Conti TTPs OH MY!
In the second half of 2021 the AT&T Managed Threat Detection and Response (MTDR) security operations center (SOC) observed an increasing number of attacks against vulnerable Exchange servers. A number of these attacks were attempting to leverage proxyshell vulnerability to gain access to customer’s networks.