Tanium Basics - Console Navigation, No Compass Needed - Tanium Tech Talks #154
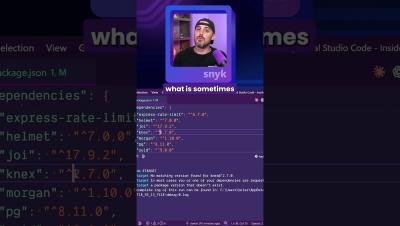
New to Tanium or just need a refresher? In this Tanium Basics kickoff episode, Jesh and Alex walk through the console UI - from environment status to modules and shortcuts - so you can navigate with confidence! What you’ll learn: Environment Status panel provides quick‑hit visibility Question Bar and Search Endpoints streamline activities Quick Links save significant time Tanium Ask enables natural language queries Modules & Shared service navigation supports core workflows Administration menus offer insight & operational controls The power of Question Builder.