Security
Antivirus Evasion for Penetration Testing Engagements
During a penetration testing engagement, it’s quite common to have antivirus software applications installed in a client’s computer. This makes it quite challenging for the penetration tester to run common tools while giving the clients a perception that their systems are safe, but that’s not always the case. Antivirus software applications do help in protecting systems but there are still cases where these defenses can be bypassed.
Egnyte Security Architecture: A Comprehensive Approach to Security
Experience integration flexibility and control with "Add by Groups"
At Egnyte, we love building new ways to help our customers use and deploy integrations within their organization. But as an organization grows, they might need more flexibility and control over which employees use which integration.
Weekly Cyber Security News 17/08/2018
A selection of this week’s more interesting vulnerability disclosures and cyber security news. Been a strange week, always is, but this time some really dumb self inflicted breaches and own goals that defy belief. What I will focus on this week is the future, the dark looming cloud that is brewing from badly thought-out out approaches to dealing with an age old problem.
Appointing a DPO
A Data Protection Officer (DPO) is a lot like a little angel on your shoulders, except instead of a little harp, they have a complete understanding of GDPR and other data protection laws. Their job is to make sure you don’t listen to the devil on your other shoulder encouraging you to do all sorts of non-compliant things, like process data unlawfully or without permission.
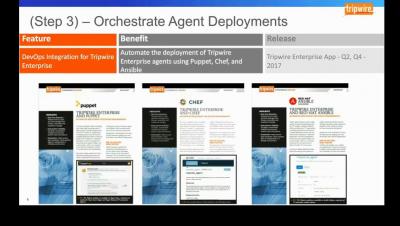
ITIL, Problem Management and Tripwire Enterprise
I’ve written about ITIL and Tripwire Enterprise, offering a secure approach to managing your Change Management processes, but ITIL’s guidelines offer more than just recommendations around ensuring changes happen as expected. Problem management is another key area where Tripwire Enterprise can help you on your ITIL journey. ITIL sensibly focuses on root-cause analysis for problem management.