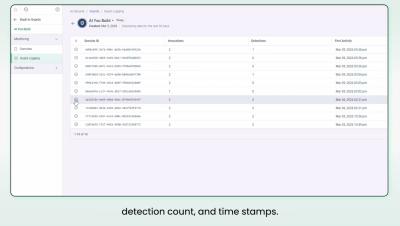
Survive the AI Code Blizzard: Introducing Snippet Detection
In 2026, software development speed is an AI-solved problem. Yet, as AI-generated code volumes surge, organizations face a new kind of risk visibility gap. Developers are increasingly copying third-party snippets into their codebases—from both AI prompts and open-source software components—creating large security and compliance blind spots that lead to significant risks.