A CISO's Guide to API Security
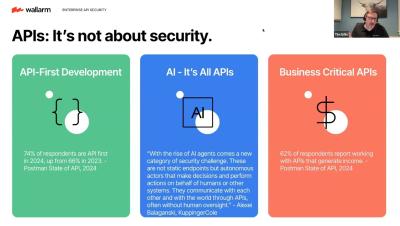
APIs are powering digital transformation but also exposing organizations to new risks. Securing them requires collaboration between CISOs, CIOs, and the board. This webinar will demystify the evolving API threat landscape, outline governance strategies, and provide leaders with the tools to communicate API risk in business terms. Key Learnings: Why You Should Attend.