Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Learning application security by finding and fixing insecure code in OWASP NodeGoat
Wouldn't it be great if we, developers, learn about application security by training on purposely-built vulnerable applications rather than finding our mistakes in production? Yes, we think so too. In this session, we welcome Priscila Oliveira, Software Engineer at Sentry and core contributor of open source npm proxy project Verdaccio, to chat about her appsec experiences as developer, and learn together about secure coding practices, how to hack a live application, open source vulnerabilities and how to fix them.
Flexible Pricing to Address the Evolving MSP Business
As MSPs prepare for the shift to hybrid work environments, it is more important than ever to have the pricing and packaging model you and your customers need. The more options you have, the more competitive you can be in the market. It's critical that service providers find vendors the flexibility you need to scale your business.
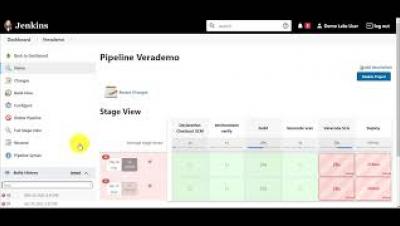
Use the Jenkins Credentials Binding Plugin to Protect Your Veracode Credentials
In this video, you will learn how to: You can use the Jenkins Credentials Binding Plugin to hide your Veracode API credentials from the Jenkins interface and logs. You use the plugin to associate, or bind, your Veracode API credentials to environment variables and save them to the Jenkins credentials store. During a build, Jenkins uses the environment variables to secretly access your credentials. The Jenkins interface and logs only show the bound environment variables.
Protecting and Managing Microsoft 365 Data
Microsoft 365 provides tools to assist with compliance, but they don’t provide native backup and recovery - they recommend customers backup their data with third-party applications. Rubrik’s SaaS-based approach to data protection for Microsoft 365 ensures critical data is secured, easily discoverable, and always accessible.