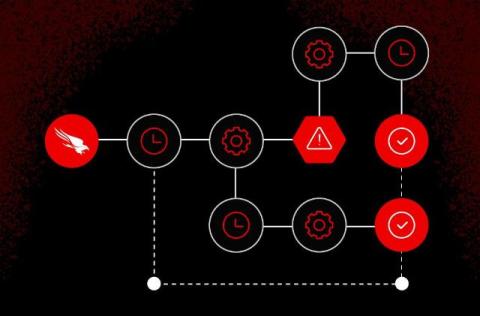
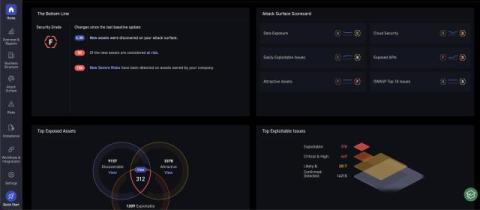
How to Scale SOC Automation with Falcon Fusion SOAR
Most SOC teams don’t struggle with what they need to automate — they struggle with where to start. Between complex playbooks, brittle integrations, and the fear of breaking something in production, security orchestration, automation, and response (SOAR) often feels harder to adopt than it should be.