Lessons Learned from OT:ICEFALL - New Vulnerabilities and Insights on OT Security Design and Patching
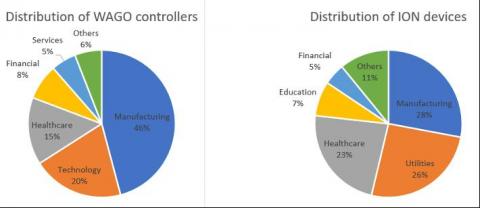
In our final OT:ICEFALL report, Forescout Vedere Labs presents three new vulnerabilities and concludes the project after one year of research following the original disclosure. The OT:ICEFALL research, including 61 vulnerabilities affecting 13 vendors, has yielded three key insights into the current state of OT product security.