Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How Transparency Can Stop Invoice Fraud
Essential Cloud Security Tools for Effective DevSecOps
How Jaguar Land Rover and Asda are Building a Modern DevSecOps Culture
New Year's security resolutions for 2024 from Snyk DevRel, SecRel, and friends
Transforming what we learned in 2023 to new learning in 2024 will be an exciting and fulfilling journey. In 2023, we saw a huge surge in the use of AI, including cyberattacks utilizing AI and machine learning. We are also seeing an increased awareness in the need for application security posture management (ASPM). Snyk has also launched its own ASPM solution — Snyk AppRisk — designed to help AppSec teams implement, manage, and scale their security programs.
Datadog's approach to DevSecOps: An executive perspective
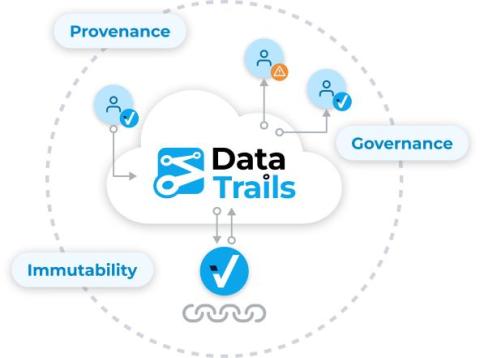
DataTrails: Sharing and Verifying Immutable Audit Trails
To share an immutable audit trail, you can do this with a link or a QR code that is automatically created when provenance and authenticity metadata is recorded in your DataTrails account. After you sign in to your DataTrails account on your smartphone, Anyone can use Instaproof or the DataTrails API to verify the authenticity, provenance and audit trails of public images.
4 Ways Veracode Fix Is a Game Changer for DevSecOps
In the fast-paced world of software development, too often security takes a backseat to meeting strict deadlines and delivering new features. Discovering software has accrued substantial security debt that will take months to fix can rip up the schedules of even the best development teams. An AI-powered tool that assists developers in remediating flaws becomes an invaluable asset in this context.