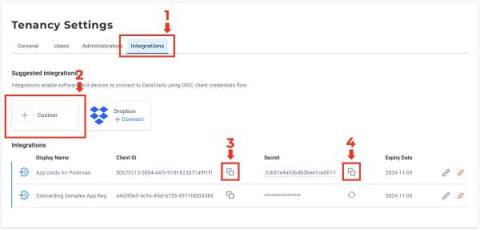
Build Audit Trails With Dropbox and DataTrails
DataTrails enables compliance and audit teams to eliminate the time-wasting and error-prone processes with our new solution. With the introduction of our Dropbox connector, there is a no-code solution that provides notarized evidence of your file’s metadata. Now you can capture legally admissible proof for your business with just a few clicks. To get started, set-up a free DataTrails account and connect it to Dropbox by following these instructions.