Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How to start a security compliance program
Security compliance programs help your organization identify, implement, and maintain appropriate security controls to protect sensitive data, comply with laws and contractual obligations, and adhere to the standards, regulatory requirements, and frameworks needed to protect customers and enable the business to succeed. In other words, with a security compliance program in place, companies are able to demonstrate that they meet designated security requirements and objectives.
ITAR and EAR Compliance in Microsoft 365 and SharePoint
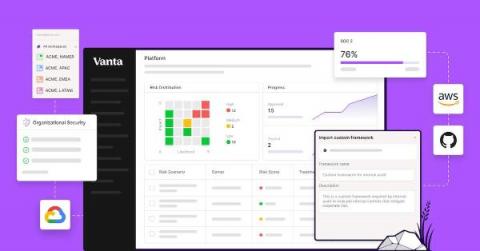
How Vanta combines automation & customization to supercharge your GRC program
As the industry’s first automated compliance platform, Vanta includes a wealth of pre-built content, which enables customers without existing compliance processes to quickly get up and running. But more mature organizations may already have a compliance program — from the processes they follow to the definitions of their compliance and security surface area — that is built to meet their unique compliance goals, auditor requirements, and tech stack.
What Your Auditor Looks for in Your Risk Management Process
TrustCloud teamed up with Dansa D’Arata Soucia on our Risk Rodeo webinar, to discuss everything you need to know to wrangle up risks with confidence. Our panelists weighed in on the four things that auditors look for in risk management processes.
CMMC Requirements For Small Businesses
There are five levels that make up the Cybersecurity Maturity Model Certification (CMMC) framework. These levels range from Level 1 (Basic Cyber Hygiene) to Level 5 (Advanced/Progressive). With each level of cybersecurity certification, the requirements of the previous level are built upon and new controls and practices are introduced.
Centralized Log Management for ANSSI and CIIP Framework Compliance
New in Vanta | June 2023
June was a month full of exciting releases for Vanta, including enhanced Risk Management customization, 21 new integrations, Automated Statement of Applicability, and more.
Risk Management Rodeo Webinar - Wrangle Risks with Confidence
FIPS 140-2: Validation VS Compliance
NIST established the crucial set of guidelines known as FIPS 140-2 to safeguard sensitive data, particularly for governmental organizations. It is to provide security and privacy when encrypting and decrypting data. The primary distinction between FIPS 140-2 validation and compliance is that. In contrast, validation involves determining if a system or product has been developed to comply with the standard’s requirements; compliance is putting those requirements into practice.