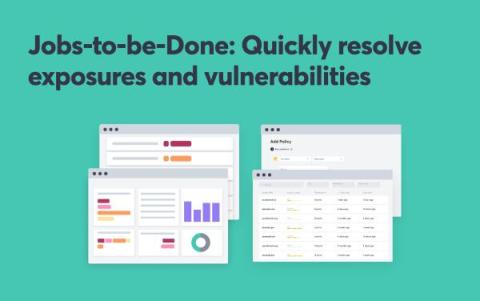
Rego for beginners: Introduction to Rego
This blog post series offers a gentle introduction to Rego, the policy language from the creators of the Open Policy Agent (OPA) engine. If you’re a beginner and want to get started with writing Rego policy as code, you’re in the right place. In this three-part series, we’ll go over the following.