Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How your screen's brightness could be leaking data from your air-gapped computer
It may not be the most efficient way to steal data from an organisation, let alone the most practical, but researchers at Ben-Gurion University in Israel have once again detailed an imaginative way to exfiltrate information from an air-gapped computer. And this time they haven’t done it by listening to a PC’s fan, or watching the blinking LED lights on a hard drive or even picking up FM radio waves.
What's Trending in 2020: Barclaycard Payment Solutions and INETCO share with Cards International
In an early January post by Mohamed Dabo of Cards International, the CEO of INETCO and the Director of Barclaycard Payment Solutions shared their views on key payment fraud and security issues that will dominate the payments landscape in 2020. Both alluded to the delicate balance between delivering an amazing customer experience, meeting compliance such as the Strong Customer Authentication (SCA) legislation, and trying to keep one step ahead of the fraudsters.
Recently found Azure vulnerabilities underline the importance of Zero-Trust for cloud workloads
Check Point researchers recently published two vulnerabilities they’d found in Microsoft’s Azure cloud services. These flaws highlight a wave of potential attacks on cloud infrastructure and the exposure of workloads running in multi-tenant cloud environments.
10 things to know about cybersecurity in 2020
Cybersecurity talent is elusive, resources are dwindling, but hacks are on the rise. We’re addressing these challenges as “must-haves” as we kick off the year is essential to an organization’s cybersecurity strategy. Here are some of the 10 things to know about cybersecurity in 2020. (If you’re interested in hearing more, register for a Cygilant and AT&T Cybersecurity webinar on the topic February 6).
Undetected E01, Johan Edholm - Evolution of hacking; Web Security to companies of all sizes.
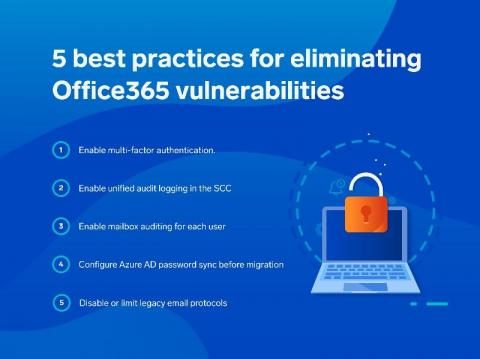
How to Secure Office365 with Cloud SIEM
Why are Security Ratings Important?
Security ratings or cybersecurity ratings provide risk management and security teams with the information needed to determine whether their vendors' and their own security posture is sufficient to prevent cyber attacks and ensure information security.
Activeboards [9] - Bounded Queries
So You Want to Achieve NERC CIP-013-1 Compliance...
Is an electricity provider’s supply chain its weakest link in the event of a cyberattack? The evidence is compelling that third parties often play unwitting roles. For example, the NotPetya ransomware attacks in mid-2017 originally gained a foothold via a backdoor in third-party accounting software. To safeguard North America’s electricity supply, the North American Electric Reliability Corporation (NERC) has issued several critical infrastructure protection (CIP) standards.
What is a SOC Framework?
In the age of the digital world, owning a Security Operations Center (SOC) is vital for the cybersecurity of every organization. However, it is not necessarily true that every SOC is effective against cyber threats and attacks. The main reason behind this fact is a lack of standardized SOC frameworks. SOC framework requires a document to be designed to provide guidelines, requirements, and specifications in order to support cybersecurity operations effectively.