Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
INETCO Insight Technical Overview - Real-time Data Acquisition, Transaction-level Monitoring and Adaptive Machine Learning Capabilities
InfoSec needs a reputation overhaul
I was in a medical office the other day, and when the doctor came into the room, he needed to unlock his phone to contact a pharmacy. I couldn’t help but notice that his home screen had a photo of an infant. It was an adorable infant, and I asked “how old is your child?” The doctor reflexively answered, “10 months”, but then became a bit shocked, and asked me ‘how do you know I have a child?".
Key security functions of unified endpoint management
As part of digital transformation, the adoption of a wide range of devices for work is on the rise. A unified endpoint management (UEM) solution is capable of enforcing management policies and configurations, as well as securing endpoints. In a previous blog, we reviewed the capabilities of a good UEM solution. In this instalment, we look at UEM security features.
HIPAA Privacy Rule Summary and Compliance Tips
The Standards for Privacy of Individually Identifiable Health Information (Privacy Rule) establishes a set of national standards for the protection of patients' rights and certain health information. Its standards address the use and disclosure of individuals' health information, known as protected health information or PHI by organizations subject to the Privacy Rule, as well as standards for an individual's rights to understand and control how their health data is used.
What is HSTS (HTTP Strict Transport Security)?
HTTP Strict Transport Security (HSTS) is a web security policy mechanism that enables web sites to declare themselves accessible only via secure connections. This helps protect websites and users from protocol downgrade and cookie hijacking attacks.
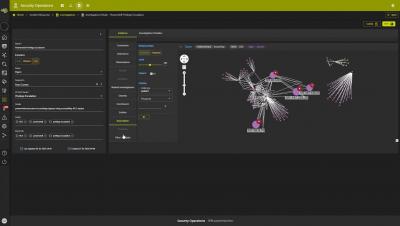
Devo Security Operations Product Introduction
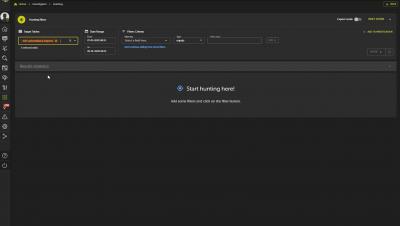
Devo Security Operations - Threat Hunting
Devo Security Operations - Alert Triage
Devo Security Operations - Investigations
Puerto Rico government falls for $2.6 million email scam
As if Puerto Rico wasn’t having a hard enough time as it attempts to recover from a recession, the damage caused by devastating hurricanes in recent years, and a damaging earthquake last month, it now finds itself being exploited by cybercriminals. According to media reports, the government of the US island territory has lost more than US $2.6 million after falling for the type of email scam that has plagued companies and organisations around the world.