Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
The MITRE ATT&CK Framework: Command and Control
Most malware these days has some level of Command and Control. This can be to exfiltrate data, tell the malware what instructions to execute next, or download encryption keys in the case of ransomware. In each case of command and control, the attacker is accessing the network from a remote location. Having insight into what is happening on the network is going to be crucial in addressing these techniques.
How Does Identity-Based Encryption Work?
With the help of breath taking technological advancements, the majority of our communications are conducted online. That is why encryption techniques are more important than ever. Keep reading to learn more about encryption techniques and identity based encryption.
A guide to penetration testing for compliance
In many cases, penetration testing – a type of ethical hacking engagement designed to identify and address security vulnerabilities in networks, systems and applications – is required. Sometimes this requirement is specified directly, while in other cases it is implied by a need to build audit or assessment processes to mitigate cyber risk. This blog identifies some of the most common pen testing standards and regulations and provides guidance about the type of testing required.
What Is Third-Party Risk Management?
Third-party risk management (TPRM) is the process of analyzing and minimizing risks associated with outsourcing to third-party vendors or service providers. This is commonly known as third-party risk or vendor risk and can include financial, environmental, reputational, and security risks due to a vendor's access to intellectual property, sensitive data, personally identifiable information (PII), and protected health information (PHI).
Ask the Experts: Building a Stronger Cybersecurity Community
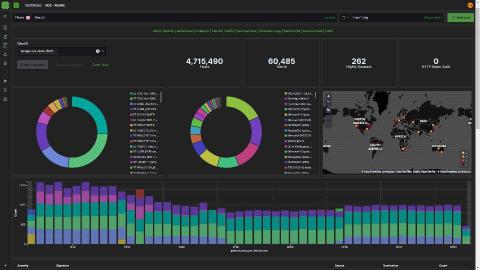
Léargas Security chooses Elastic, drops Splunk to battle COVID-19 fraud
Léargas Security (Léargas is Gaelic for “insight”) provides clients with actionable insights into anomalous or abstract behaviors through the correlation of data gathered from converged security controls: cyber and physical.
A Checklist for Effective Threat Hunting Tools
Threat hunting is one of the most critical activities performed by SOC teams. Once an alert triggers and a tier-1 analyst assesses it and sends it up the line for further evaluation by a more senior analyst, the race is on. Hunting down the threat as quickly as possible, before it can wreak havoc on the organization, becomes the top priority.
Stories from the SOC - detecting network anomalies with OTX
This Investigation was initiated on the basis of several Network Anomaly alarms triggered by ongoing suspicious activity on an employee device owned by a financial institution. During the discovery phase of the Investigation, we identified abnormal egress traffic to a known Indicator of Compromise (IOC) based on intelligence from the Open Threat Exchange™ (OTX®).
1Password Advanced Protection walkthrough
How ExpertOps Can Help You Address the Infosec Skills Gap
Are you struggling to hire skilled digital security talent in 2020? If so, you’re not alone. According to a Tripwire study on the infosec skills gap, 82% of security experts said that their teams were understaffed; nearly the same proportion (83%) indicated that they were feeling more overworked going into 2020 than they were a year prior.