Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Biggest Data Breaches in Australia (Includes 2021 Attacks)
Data breaches in Australia are on the rise, particularly in the financial and healthcare industries. In an effort to DISRUPT this pernicious trend, the Australian government is revising its cybersecurity frameworks and policies to strengthen resilience against nation-state threat actors. But Australian businesses cannot solely rely on the government's cybersecurity initiatives. Even the Australian Signals Directorate (ASD) admits that proposed security frameworks only raise the baseline of security.
The Aviation Industry Needs to Move Towards Cyber Resilience
2021 is a significant year for aviation. It marks the 20th anniversary of the 9/11 attacks, the worst acts of unlawful interference in the history of aviation. It is also the Year of Security Culture for the ICAO community, which aims to enhance security awareness and foster a security culture throughout the industry.
Kaseya, Sera. What REvil Shall Encrypt, Shall Encrypt
When Splunk told me we would have a “breach holiday” theme for the summer, I didn’t think it would be quite so on the nose… For those of you who have been working on this Kaseya REvil Ransomware incident over the weekend, I salute you. We’ve been doing the same. As usual, my team here at Splunk likes to make sure that we have some actionable material before posting a blog, and this time is no different.
MSPs Targeted in Ransomware Attack
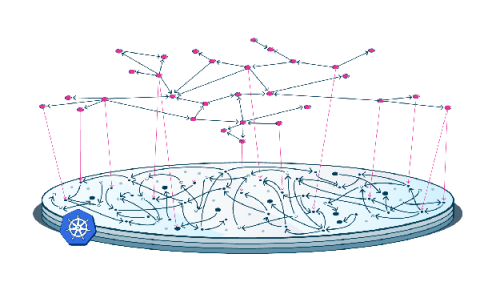
Networking with a Service Mesh: Use Cases, Best Practices, and Comparison of Top Mesh Options
Service mesh technology emerged with the popularization of microservice architectures. Because service mesh facilitates the separation of networking from the business logic, it enables you to focus on your application’s core competency. Microservice applications are distributed over multiple servers, data centers, or continents, making them highly network dependent.
Atlas Inside and UTMStack Solutions
The Buyer's Guide to Scalable Application Security
Detectify is helping tech organizations bring safer web products to market by providing crowdsourced, cloud-based, continuous web app security. Here’s a buyer’s guide on how you can get scaleable application security in 2021 and beyond. There are so many appsec tools out there with the same features. It’s hard to see value clearly amongst all the noise.
Weekly Cyber Security News 02/07/2021
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. While the sensitive security documents were reported as lost, the published reason as to why saying it is not know sounds rather suspicious. I fully expect this will be brushed under a bush somewhere – much like the documents.
Verify and Validate Zero Trust Architecture
With the constant rise of modern cyber threats, many businesses are aiming for zero-trust infrastructure to keep themselves and their customers safe. But a zero-trust environment, where only authorized people can access information and resources, is often more difficult to implement than anticipated. If security teams and network engineers cannot visualize the network and its possible traffic paths and behaviors, they can’t possibly secure the environment.
Top 5 Scam Techniques: What You Need to Know
Scammers are increasingly resourceful when coming up with scam techniques. But they often rely on long-standing persuasion techniques for the scam to work. So, you may hear about a new scam that uses a novel narrative, but there is a good chance that the scam relies on proven scam techniques once the narrative is stripped away. These scam techniques often exploit our characteristics and heuristics, or things that make us human and fallible.