Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Drive Fast, Drive Safe... Creating the Halo Effect in your Security Programme
In 2018, as followers of Formula One (F1) will know, the fastest racing cars in the world got a controversial redesign. A new device was added to the cars; a curved bar or Halo, which was designed to protect the drivers’ heads in the event of a crash.
Zapier Storage Exposes Sensitive Customer Data Due to Poor User Choices
Zenity research team has recently discovered a potential customer data leakage in Storage by Zapier, a service used for simple environment and state storage for Zap workflows. With only a few simple steps and no authentication, we were able to access sensitive customer data. Given the nature of this flaw, it would be easy for bad actors to recreate our approach and access the same sensitive data without significant expertise.
Cloud Configuration Drift: What Is It and How to Mitigate it
More organizations than ever run on Infrastructure-as-Code cloud environments. While migration brings unparalleled scale and flexibility advantages, there are also unique security and ops issues many don’t foresee. So what are the major IaC ops and security vulnerabilities? Configuration drift. Cloud config drift isn’t a niche concern. Both global blue-chips and local SMEs have harnessed Coded Infrastructure.
How Zero Trust Strengthens Password Security
Password security is crucial to preventing cyberattacks. It is important to find a password manager that enables the zero-trust security model to mitigate the risks of data breaches from compromised user accounts. The U.S. government released a memorandum earlier this year, detailing the requirement for federal agencies to achieve zero trust by the end of Fiscal Year 2024 in an effort to strengthen their cyberdefenses.
Cyber Security Professionals Shortage, Burnout & How To Protect Against It | Razorwire Podcast
The Evolution Of Cyber Security & Trends To Watch For | Razorwire Podcast
The Future Of Security For Working From Home - Razorwire Podcast
Where a CISO Should Sit Within an Organisation - Razorwire Podcast
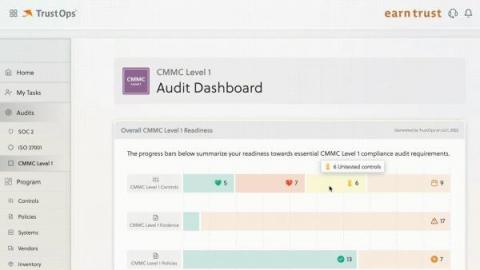
Kintent Trust Cloud Supports CMMC Level 1
Achieving CMMC compliance is no easy feat. CMMC requirements are stricter than most, and focus heavily on documentation. This certification is also still relatively new, so it’s constantly undergoing changes.
Clearing the air over the new CERT-In rules
Authorities that lay down compliance regulations often update them in order to keep them relevant. However, for organizations that fall under the purview of these regulations, it can be a challenge to keep up with the updates and ensure that they stay compliant.