Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
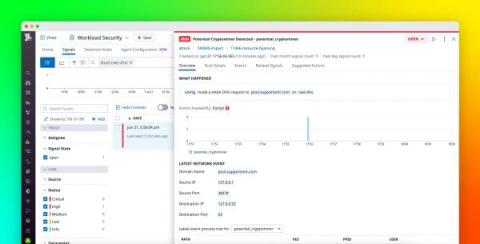
Identify security vulnerabilities with DNS-based threat detection
The Domain Name System (DNS) is responsible for mapping client-facing domain names to their corresponding IP addresses, making it a fundamental element of the internet. DNS-level events provide valuable information about network traffic that can be used to identify malicious activity. For instance, monitoring DNS lookups can help you see whether a host on your network attempted to connect to a site known to contain malware.
Are your credentials safe? Decoding credential phishing attacks
Companies have increasingly allowed bring your own device (BYOD) policies to support remote work, but in today’s cybersecurity landscape, this trend has led to an increased attack surface. Each additional endpoint increases the potential for credentials to be compromised through credential phishing attacks. Hackers are leveraging this trend to conduct insider attacks, leaving businesses vulnerable to data breaches.
WatchGuard Honored in CRN's First-Ever MES Matters List for 2022
We are thrilled to announce that CRN has recognized WatchGuard in its first-ever MES Matters list for 2022! This awards program highlights vendors that have proven themselves to be cutting-edge technology providers offering solutions that support the growth and innovation of midmarket organizations. CRN defines the midmarket as an organization with an annual revenue of $50M - $2B, and/or 100 – 2500 total supported users and seats.
Weekly Cyber Security News 01/07/2022
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. Often a target for directory traversal, file packing utilities offer an excellent way to break a system. Sandboxing is a good test first but who regularly does that?
How CrowdStrike's Machine Learning Model Automation Uses the Cloud to Maximize Detection Efficacy
At CrowdStrike, we combine cloud scale with machine learning expertise to improve the efficacy of our machine learning models. One method for achieving that involves scanning massive numbers of files that we may not even have in our sample collections before we release our machine learning models. This prerelease scan allows us to maximize the efficacy of our machine learning models while minimizing negative impact of new or updated model releases.
NIST updates guidance on supply chain risk
How to Identify Timestomping using KAPE
What is Firewall Logging and Why is it Important?
Firewall logging is an important piece of your advanced security strategy. A firewall is a security system that helps protect your computer or network from unauthorized access. One important function of a firewall is to log information about each connection attempt, including who attempted to connect and when.