Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Keeper 101 - Native App Filler
Keeper can automatically fill fields in any native application using a set of custom keystrokes.
Instant Zero-Trust Access to Remote IT Infrastructure
Tired of the latency, availability and reliability issues of VPNs and legacy remote desktop tools? Keeper Connection Manager (KCM) provides DevOps and IT teams with effortless access to RDP, SSH, database and Kubernetes endpoints through a web browser on any device. Watch this webinar to learn more about KCM and how you can grant access to privileged systems without exposing login credentials. During the webinar, Zane Bond, Sr. Director of Product Management, will cover.
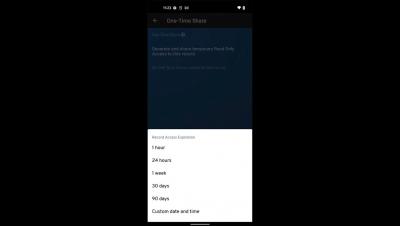
Keeper One-Time Share for Android
Keeper "One-Time Share" provides time-limited, secure sharing with anyone, even if they don’t have a Keeper account. One-Time Share is the most secure way to send confidential information to a friend, family member or co-worker without exposing sensitive information in plain text over email, text message or messaging. To share a record using One-Time Share on an Android device, select the record and tap Share. From the options, select One-Time Share. Next, tap the One-Time Share icon in the lower right corner of your screen and select your preferred record access expiration.
Remote Users - Protection from Internet-Based Threats
When working remotely, users are susceptible to Internet-based threats like phishing and malware. With the Lookout Security Service Edge (SSE) platform, organizations can prevent the loss of personal information and the installation of malware by assessing each link a user tries to access, regardless of what doc or app contains the link.
Remote Users - Protect Data within Managed Apps
Organizations need to maintain security controls on corporate data regardless of where the users work location. When uploading content to a cloud storage provider, the Lookout SSE platform can help direct users to use corporate providers instead of personal. And when data is downloaded locally, the Lookout platform can protect the data outside of the managed app through encryption.
Remote Users - ZTNA to Private Enterprise Apps
When working remotely, users still require access to private enterprise apps. With the use of a Zero Trust Network Access (ZTNA) solution, users gain instant access to the app without installing, configuring, and launching a VPN connection.
PCI DSS & Virtualization
Virtualization is a technology that has greatly benefited businesses around the globe. The technology has a significant impact on the modern IT landscape and today plays a key role in the development and delivery of cloud computing solutions. However, the adoption of this advanced technology has major security implications on businesses today. The adoption of Virtualization has opened doors to a broad range of challenges for businesses in the industry. Especially, for organizations that are PCI regulated and required to comply with PCI DSS Standards, the challenges in this area only seem to grow.
GDPR Compliance Checklist
General Data Protection Regulation (GDPR) is a global data privacy law established and enforced in the EU. It is a comprehensive law developed to protect and uphold the rights of EU Citizens. Organizations dealing with the personal data of citizens of the EU are required to comply with the requirements of GDPR. This brings in more transparency in the processing and securing of personal data while also ensuring citizens have control over their personal data.
ISO 27001 Checklist And Security Controls
Information Security Management System is an international standard designed to manage the security of sensitive information. At the core, ISMS is about managing the people, processes, and technology through a risk management program. While there are many standards under the ISO27000 family, the ISO27001 Standard is the most popular and widely accepted standard in the industry.
The Key to Risk Intelligence: Visibility
Not all cybersecurity vulnerabilities are created equal. Some vulnerabilities have the potential to bring the entire organization to a halt, such as in the case of ransomware. Meanwhile, other vulnerabilities may only create limited opportunities for exploitation, putting them lower on the list of things to patch.