Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Top 10 Law Enforcement Operations Against Cyber Crime in 2022
Since the start of 2022, multiple law enforcement agencies worldwide have been taking action targeting organized cyber crime activity, including cyber criminals behind phishing and BEC scams, dark web forums, or malware distribution. Here’s Top 10 of the most notable law enforcement ops against cyber crime carried out in the past ten months.
Supply chain integrity, transparency and trust is now firmly on the agenda
Supply chain risk continues to make headlines, from Solarwinds and Kaseya to last week’s announcement of a patch for the OpenSSL vulnerability, and the latest cybersecurity review from the U.K.’s National Cyber Security Centre highlights the serious threats posed by supply chain attacks.
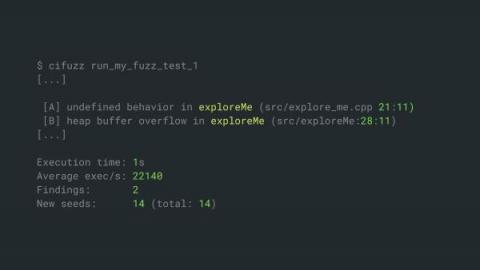
Secure Coding in C and C++ Using Fuzz Testing
Today, I would like to show you to a simplified fuzz testing approach that enables secure coding of C and C++ applications. If you read this article to the end, you will learn about an automated security testing approach for C/C++ that can protect your applications against all sorts of memory corruptions and other common C/C++ vulnerabilities.
How to navigate 1Password like a pro with Quick Access
We like to get things done at 1Password, which is why we’re such big fans of Quick Access in 1Password 8.
Cyber Attacks Are Coming, Cyber Security Must Ensure Business Survivability
Detecting 5 current APTs without heavy lifting
The Corelight Labs team prides itself on the ability to create novel Zeek and Suricata detection content that delves deep into packet streams by leveraging the full power of these tools. However this level of additional sophistication is not always required: sometimes there are straightforward approaches that only require queries over standard Zeek logs. It’s always valuable when developing detections to keep in mind that “sometimes simple does just fine.”
Budget and momentum are key to cybersecurity automation maturity - and CISOs are feeling left behind
As cyber threats intensify and the human and financial resources available to deal with them remain limited, there is a growing need for automation in cybersecurity. The intelligent automation of key cybersecurity processes can significantly improve an organization’s posture and at the same time support under-pressure employees by reducing reliance on manual processes.
Developing an Effective Change Management Program
Change detection is easy. What is not so easy, is reconciling change. Change reconciliation is where most organizations stumble. What was the change? When was it made? Who made it? Was it authorized? The ability to answer these questions are the elements that comprise change management. Historically, the haste of accomplishing a task consisted of a sysadmin moving full-speed ahead to satisfy the needs of the business.
How to deal with ransomware on Azure
Let’s dig deeper into the techniques used by attackers and the mitigations you should implement when ransomware on Azure affects you. By now, we should all be aware of ransomware from the constant news articles associated with this known threat. As we explained in the anatomy of a cloud attacks, ransomware is a way for attackers to make money when they gain control of your accounts through data encryption, therefore restricting your access to the system.
The state of SOAR: Tines survey reveals the pros and cons of SOAR platforms
The SOAR market is undergoing a radical transformation fueled by the rise of best-in-class tools that are laser-focused on helping security teams to solve a core problem. Until recently, SOAR was driven by all-in-one solutions, claiming to be silver bullets but offering suboptimal functionality and user experiences.