Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Why Traditional DLP Fails in the Age of Cloud and Collaboration Tools
DLP emerged at a time when corporate IT environments were relatively straightforward. Employees worked primarily from corporate offices, data resided in on-premises servers, and communications happened through company-managed email systems and file shares. Traditional DLP solutions were designed to thrive in this environment.
Trustwave MXDR and Co-Managed SOC: Revolutionizing Cybersecurity
As organizations continue to face an increasing number of sophisticated threats that require advanced managed detection and response capabilities, Trustwave has developed a series of solutions to help maintain a high level of security. One such solutions is Trustwave’s Managed Extended Detection and Response (MXDR) with Co-Managed Security Operations Center (SOC) offering.
ISO 27017 Cloud Controls: List of Tasks for Providers
Most of the time on the Ignyte blog, we talk about overarching security frameworks like FedRAMP, CMMC, and ISO 27001. Sometimes, though, it’s worth digging deeper into smaller-scale elements of these frameworks. Today’s target is ISO 27017, the ISO/IEC publication focusing on cloud service security. What does this document entail, who needs to use it, and what does compliance involve? Let’s discuss.
8 Most Common Password Mistakes
Password mistakes are a widespread issue and expose you to many cybersecurity risks. Watch this video to learn about the common password mistakes people make and how to fix them.
Does a VPN Protect You From Hackers?
Can a Virtual Private Network (VPN) really protect you from hackers? While VPNs encrypt your internet traffic and hide your IP address, they don’t make you invincible online. In this video, we break down which cyber threats VPNs can and can’t protect you from — plus tips to keep your accounts and devices secure.
You Don't Need College to Succeed in #Cybersecurity #careerintech
Mend.io, formerly known as Whitesource, has over a decade of experience helping global organizations build world-class AppSec programs that reduce risk and accelerate development -– using tools built into the technologies that software and security teams already love. Our automated technology protects organizations from supply chain and malicious package attacks, vulnerabilities in open source and custom code, and open-source license risks.
Small Companies vs. Big Expectations
On the podcast: Small organisations face real constraints in DORA rollout, but the law doesn’t bend.
Why Legacy DLP Fails: The Hidden Data Risks You Can't See
Legacy data loss prevention (DLP) tools were built for a different era—a time when data sat safely behind firewalls and security meant scanning files for keywords. But today, data moves across cloud apps, personal devices, and collaboration tools faster than ever. Legacy DLP simply can’t keep up. In this video, we break down: If your organization is still relying on outdated DLP systems, it’s time to evolve. Because what your tools can’t see will hurt you.
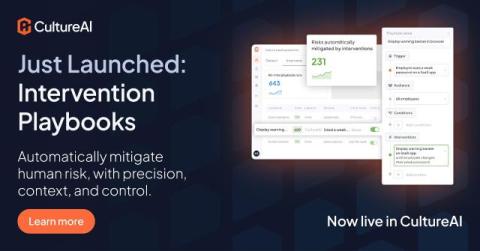
Just launched: Interventions Playbooks - context aware security automation
Security Operations Centre (SOC) teams have never had it easy - but today, the complexity of defending against cyber threats has taken on an entirely new dimension. You’ve secured endpoints, networks, and cloud infrastructure. But the biggest threats are at the human layer, where visibility is lacking and most breaches begin.