Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
How SOCs can level up their PCAP game with Smart PCAP (Part 2)
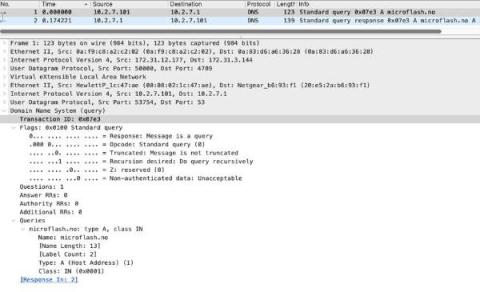
In terms of unencrypted traffic, several highly used protocols lend themselves to logging and can significantly reduce the burden of packet capture without lowering the fidelity of information or the capabilities of analysts.
Tutorial: Cyclops Blink Detection Tools
Detection as Code: How To Embed Threat Detection into Code
Threat Detection In 2023 Is Broken. Here's How to Fix It
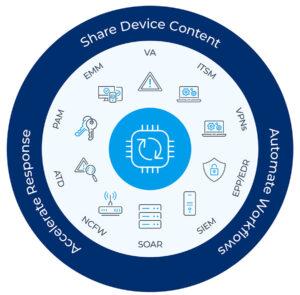
Why have cyber incidents topped the Allianz Risk Barometer for the last two years in a row? Growing attack surfaces are partly responsible. Remote work, cloud migration, IoT use and other trends give cyber threats more places to enter and hide within networks. But there is another cause – deficiencies in the standard approach to threat detection and response.
5 Steps to Combating Emerging Threats with Network Security
In today’s rapidly evolving threat landscape, cybercriminals have become more sophisticated than ever, making it crucial to stay abreast of the latest trends and tactics. The challenge is exacerbated by the expanding attack surface as more devices and device types connect to enterprise networks: IT, OT, IoT and IoMT devices, all with known vulnerabilities that can be exploited.
Ransomware detections on endpoints increase by 627%
Ransomware is still present and growing across the threat landscape, to the extent that some organizations now include the cost of a ransomware attack in their annual budgets. Data from our Internet Security Report - Q4 2022 reveals that ransomware detections on endpoints rose by an alarming 627% in 2022 compared to the previous year. While ransomware does not discriminate by industry type, the report clearly shows the manufacturing sector was the most affected during 2022.
What are Advanced Persistent Threats (APT) and How to Prevent Them.
Extending visibility through our new ICS/OT collection
Increasingly, security teams are tasked with identifying, understanding, and managing risk around devices that may live outside the traditional IT umbrella. Operational Technology (OT) refers to computing systems that are used to manage and process operational functions as opposed to administrative operations, with Industrial Control Systems (ICS) being a major segment of that OT sector.