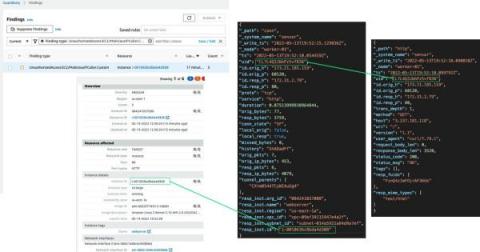
Detections and Findings using Corelight in the Black Hat Asia NOC
As promised, we wanted to dedicate a blog to detections and findings from the network operations center (NOC) at Black Hat Asia 2023 as a follow up to our Lessons Learned blog. Some of these discoveries may not surprise the seasoned analyst or senior threat hunter – but will hopefully provide a little entertainment, because the more things change, the more they stay the same.