Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
DeepSeek Just Shook Up AI. Here's How to Rethink Your Strategy.
The rapid rise of generative AI (genAI) applications is reshaping enterprise technology strategies, pushing security leaders to reevaluate risk, compliance, and data governance policies. The latest surge in DeepSeek usage is a wake-up call for CISOs, illustrating how quickly new genAI tools can infiltrate the enterprise. In only 48 hours, Netskope Threat Labs observed a staggering 1,052% increase in DeepSeek usage across our customer base.
Quantum Computing Leaders in 2024: Which Companies Are Leading the Way?
Quantum computing is no longer a topic of science fiction but rather very real, and in 2024, the race to harness the power of quantum mechanics for computational purposes is fiercer than ever, with major players from both the tech industry and specialized startups pushing the boundaries of what is possible. Quantum technologies have inched a step further toward practical realities. A set of firms has surfaced and leads this transformation, changing the course.
The Hidden Biases in Your AI
"Bias" might sound simple, but in AI, it's anything but. Here's the reality: AI isn't free of prejudice; instead, it reflects it-sometimes in surprising and troubling ways. A quote from IBM's Francesca Rossi captures it well: "AI is a reflection of our humanity. When we don't address biases, we don't just create flawed machines; we amplify our own inequalities." This concept isn't just a philosophical idea; it's an observable and urgent issue.
Cloudflare launches One-Click content credentials to track image authenticity and preserve creator attribution
Industry-first solution now allows publishers and media organizations to preserve the digital history of their images across Cloudflare's global network.
Best LLM Security Tools of 2025: Safeguarding Your Large Language Models
As large language models (LLMs) continue to push the boundaries of natural language processing, their widespread adoption across industries has highlighted the critical need for robust LLM security solutions. These powerful AI systems, while immensely beneficial, are vulnerable to emerging threats such as data leakage, prompt injection attacks, and compliance risks. In 2025, the landscape of LLM security tools has evolved to address these unique challenges, ensuring their safe and responsible deployment.
The Future of Cloud Computing: What's Next for Businesses and Technology?
The future of cloud computing is expected to drive innovation, efficiency, and security in the future, transforming both organizations and technology. Faster processing, improved security, and more intelligent automation are becoming more and more necessary as businesses depend more and more on cloud infrastructure.
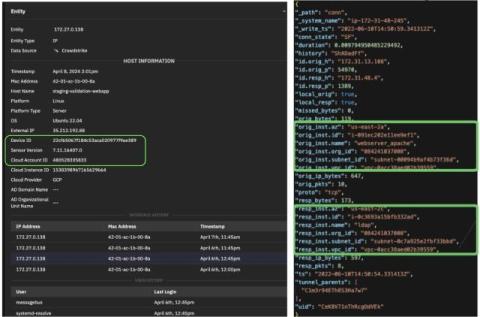
Why NDR is essential to protecting your cloud workloads
How Corelight Open NDR secures cloud workloads beyond runtime security tools.
DeepSeek DDoS: Why AI Needs Machine Identity Security
Imagine a sleek, high-tech sports car racing downhill without brakes. Now, imagine that car is actually the AI driving your business. Powerful yet precariously close to catastrophe. That’s why, as we accelerate AI adoption, including AI agents, we can’t afford to overlook security guardrails. This fact was front and center during the recent “large-scale cyberattack” on DeepSeek, a strategic open-source AI player from China that’s been disrupting the global AI space.
Behind the scenes of Elastic Security's generative AI features
A quantitative approach to prompt tuning and LLM evaluation Elastic has long been developing machine learning (ML) and AI-powered security detections. We constantly bring in new technologies when available to help make our users’ lives easier. So, with the rise of generative AI (GenAI), we have developed even more Elastic Security features to use this powerful, new technology. Among those are.