Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Fixing Credit Card Hack in OpenCart Store - Step-By-Step Process From Locating to Malware Removal
Veracode State of Software Security: Half of Application Security Flaws Remain Open Six Months After Discovery; Apps with Technical Debt Take Two Times as Long to Fix
Duped, deluded, deceived: How disinformation defrauds you
The rise of social media has no doubt been one of the major revolutions of the 21st century. It’s brought about a whole new way for people to connect and share information with others, regardless of their geographical locations. But along with these more noble intentions of social media, there will always be abuse of these platforms – and one of the big ones is the spread of disinformation.
njRAT Rising - The Increase in Activity of the Remote Access Trojan
First identified as active in November 2012, 'njRAT', also known as 'Bladabindi' or 'Njw0rm', is a well established and prevalent remote access trojan (RAT) threat that was initially created by a cybercriminal threat group known as 'Sparclyheason' and used to target victims located in the Middle East. Undoubtedly following the source code leak, reportedly in May 2013, njRAT has become widely available on the cybercriminal underground with numerous variants being released over the years.
Web Cache Entanglement - Novel Pathways to Poisoning
Each year we anticipate new research from James Kettle at the annual Black Hat USA event and he’s become known for his web cache research. This year he announced Web Cache Entanglement – new techniques to exploit web cache poisoning. We’ve previously covered his work concerning web cache poisoning and HTTP request smuggling which is intriguing for any software engineer to know about. This article will briefly highlight the main points about Web Cache Entanglement.
SOC 2 compliance for containers and Kubernetes security
This article contains useful tips to implement SOC 2 compliance for containers and Kubernetes. The Service Organization Controls (SOC) reports are the primary way that service organizations provide evidence of how effective their controls are for finance (SOC 1) or securing customer data (SOC 2, SOC 3). These reports are issued by the American Institute of Certified Public Accountants (AICPA).
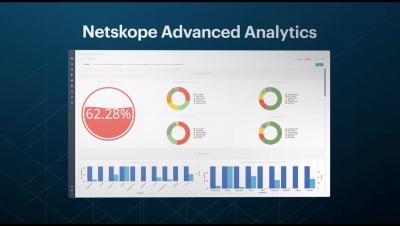
Introducing Netskope Advanced Analytics
Introducing Advanced Analytics
Every organization is adopting the cloud, but there are some companies that are reaping a larger number of benefits from cloud transformation than others. Making an effort to adopt the cloud is simply not enough to realize the benefits. The organization that prepares for efficiently managing risk will be able to capture a larger percentage of the benefits than one that has not.