Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Instant Zero-Trust Access to Remote IT Infrastructure
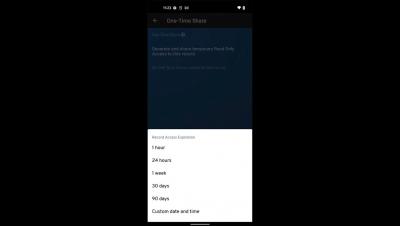
Keeper One-Time Share for Android
Remote Users - Protection from Internet-Based Threats
Remote Users - Protect Data within Managed Apps
Remote Users - ZTNA to Private Enterprise Apps
The Key to Risk Intelligence: Visibility
Not all cybersecurity vulnerabilities are created equal. Some vulnerabilities have the potential to bring the entire organization to a halt, such as in the case of ransomware. Meanwhile, other vulnerabilities may only create limited opportunities for exploitation, putting them lower on the list of things to patch.
Penetration Testing in 2022: Key Trends and Challenges
Just when you thought that we couldn’t be any more integrated with (and dependent on) technology, the Covid pandemic swooped in to prove otherwise. The rise in the use of applications and devices to perform even basic functions pushed companies and end-users to keep pace. Of course, one group of people always seem to be ready: cybercriminals. Cyber attacks are steeply increasing, and attackers are cunning, always finding new ways to get what they want.
How to Secure a Service Mesh Architecture
Many organizations build applications using microservices that often communicate with other distributed services. Ensuring that they remain secure requires a “secure token service,” secure communication protocols (mTLS), authentication, authorization, and data encryption.
Managing Microsoft 365 Guest Access
Speaking with clients, I find one of the biggest issues they struggle with how to properly secure Guest access in Microsoft 365 applications. While many organizations had already begun outsourcing their email to M365, most had really only begun looking at the rest of the M365 offering (Teams, SharePoint Online and OneDrive) when COVID hit. Most organizations wound up diving headfirst into this offering in an attempt to deal with the sudden need to work and collaborate with colleagues from home.