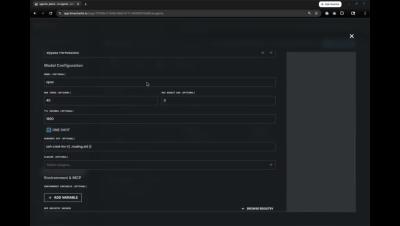
AI SecOps Worskhop Series: Detection Engineering with LimaCharlie and Claude Code
This hands-on workshop is designed for security professionals interested in learning how to integrate advanced AI capabilities into their detection and response workflows. Attendees will receive practical, step-by-step instruction on leveraging the power of Claude Code, a sophisticated AI agent, to significantly enhance security operations within the LimaCharlie platform for detection engineering use cases.