Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Understanding Cyber Threat Intelligence
“If you know the enemy and know yourself, you need not fear the result of a hundred battles. If you know yourself but not the enemy, for every victory gained you will also suffer a defeat. If you know neither the enemy nor yourself, you will succumb in every battle.” – Sun Tzu. The above quote by Sun Tzu summarizes cyber threat intelligence (CTI) perfectly.
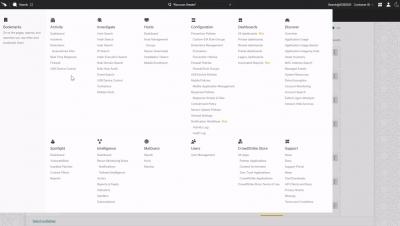
Spear Phishing Triage Using ThreatQ and TDR Orchestrator
According to Proofpoint’s 2021 State of the Phish Report, more than 80% of organizations fell victim to a phishing attack last year. Another report from PhishMe found that 91% of cyberattacks start with a phish, and the top reasons people are duped by phishing emails are curiosity (13.7%), fear (13.4%), and urgency (13.2%), followed by reward/recognition, social, entertainment, and opportunity.
ThreatQuotient Enhances Data-Driven Automation Capabilities with New ThreatQ TDR Orchestrator Features
CrowdStrike Falcon Intelligence Recon
Top 10 Cyber Threat Intelligence Tools for 2022
Cyber threat is soaring on the list of the gravest challenges plaguing organizations today. This is partly an outcome of developers including security in their development process as an afterthought. Although enterprises quickly realize the cyber threat risks to their businesses and reputation, they seem to be in a state of indecision.
Organizations are traveling the road to cybersecurity automation, but it is not a smooth journey
Our latest industry research – ‘The 2022 State of IT Security Automation Adoption’ – which we have undertaken for the second year running and expanded into other regions including the UK, USA and Australia, shows strong signs that cybersecurity automation adoption is advancing, but 97% of respondents say they have experienced problems during implementation.
The Cycle: Global Threat Dynamics
Unlock the Power of Security Automation: Threat Intelligence Management
Threat intelligence has become a significant input to the overall ecosystem that organizations leverage in their security footprint. Managing that data and the contextualization required to develop useful information can be daunting for fledgling and established organizations. I will discuss ways to automate some of the repetitive tasks and fuel other areas of the security organization to help them better achieve their mission sets.