Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Unlock the Power of Security Automation: 3 Use Cases to Consider
At ThreatQuotient, we write a lot about security automation. Most recently, we’ve discussed how our data-driven approach to automation helps enable extended detection and response (XDR) in all phases of security operations including detection, investigation and response.
As the Cyber Threat Environment Escalates, How are Organizations Responding?
Globally, the cyber threat level to organizations remains high and the current situation only serves to highlight this further. To this point, any organization that has substantial gaps in its cybersecurity capabilities is operating at risk, and when the threat landscape changes, as it has now, so we become more aware of the vulnerabilities that we have carried for some time and the need for better Cyber Threat Intelligence.
Using Threat Intelligence To Advance Your Security Posture
People often ask me, “What’s the purpose of cybersecurity?” I tell them that it serves to protect the valuable, intangible data assets of firms or private individuals, usually by trying to shrink the attack surface. One way to achieve cybersecurity is to utilize threat intelligence research in your firm’s security plan. In this article, I will discuss the benefits of understanding and implementing a threat intelligence program.
Automation in Cybersecurity: Overcoming Barriers to Adoption
“Automation” has become a buzzword in cybersecurity circles. That’s not surprising in an environment where security specialists are in short supply and under intense pressure to defend the business against a huge variety of threats from innumerable different sources. Using technology to do at least some of the work seems like a no-brainer. Nevertheless, it seems that organizations are finding it hard to get the right approach to cybersecurity automation.
Correlating Data across Multiple Security Systems and Tools with XDR
Gartner defines Extended Detection and Response (XDR) as “a SaaS-based, vendor-specific, security threat detection and incident response tool that natively integrates multiple security products into a cohesive security operations system that unifies all licensed components”. Simply put, the main component of XDR is the ability to correlate data across multiple security systems and tools for better detection and response.
Walt & Company: Staying Ahead of the Curve
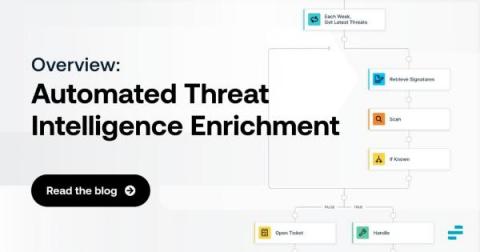
Automated Threat Intelligence Enrichment: An Overview
Discovering security threats is good and well. But, in many cases, simply knowing that a threat may exist is not enough. Instead, you also need threat intelligence enrichment. Threat enrichment plays a critical role in helping to evaluate and contextualize threats, root out false positives and gain the insights necessary to mitigate risks as efficiently and quickly as possible.